-
Manage your Success Plans and Engagements, gain key insights into your implementation journey, and collaborate with your CSMsSuccessAccelerate your Purchase to Value by engaging with Informatica for Customer SuccessAll your Engagements at one place
-
A collaborative platform to connect and grow with like-minded Informaticans across the globeCommunitiesConnect and collaborate with Informatica experts and championsHave a question? Start a Discussion and get immediate answers you are looking forCustomer-organized groups that meet online and in-person. Join today to network, share ideas, and get tips on how to get the most out of Informatica
-
Troubleshooting documents, product guides, how to videos, best practices, and moreKnowledge CenterOne-stop self-service portal for solutions, FAQs, Whitepapers, How Tos, Videos, and moreVideo channel for step-by-step instructions to use our products, best practices, troubleshooting tips, and much moreInformation library of the latest product documents
-
Rich resources to help you leverage full capabilities of our productsLearnRole-based training programs for the best ROIGet certified on Informatica products. Free, Foundation, or ProfessionalFree and unlimited modules based on your expertise level and journeySelf-guided, intuitive experience platform for outcome-focused product capabilities and use cases
-
Library of content to help you leverage the best of Informatica productsResourcesMost popular webinars on product architecture, best practices, and moreProduct Availability Matrix statements of Informatica productsMonthly support newsletterInformatica Support Guide and Statements, Quick Start Guides, and Cloud Product Description ScheduleEnd of Life statements of Informatica productsMonitor the status of your Informatica services across regions
- Solution Accelerators
- General Data Protection Regulation
The General Data Protection Regulation (GDPR) is considered to be the most stringent privacy and security law in the world at the heart of which is that individuals have the right to be informed about the collection and use of their data.
Privacy is key to reinforcing user trust. Our GDPR accelerator charged with example-based content will help you implement privacy by design and achieve and maintain compliance.
Our GDPR Accelerator provides Informatica Data Privacy Framework with prefilled templates to showcase how sensitive data moves across the onboarding process. We offer exercises with another tool called Data Privacy Management (DPM) to check whether sensitive data is protected. We also have Workflows that you can customize. We cover main use cases like Subject Rights Requests (SRR), Data Subject Access Request (DSAR), Right To Be Forgotten (RTBF), and Right to Rectification. With our GDPR Accelerator, you can be prepared to tackle compliance.
Through this GDPR accelerator, you saw example-based content helping you implement privacy by design and achieve and maintain compliance.
The module provided Informatica Data Privacy Framework with prefilled templates that showcased how sensitive data moves across the onboarding process. There were exercises with Data Privacy Management (DPM) to check whether sensitive data is protected. You also had Workflows that you can customize and covered major use cases like Subject Rights Requests (SRR), Data Subject Access Request (DSAR), Right To Be Forgotten (RTBF), and Right to Rectification.
Contents


Data governance is a set of principles and practices that ensure high quality through the complete lifecycle of your data.
Disclaimer:
The GDPR accelerator is an example-based content and may differ from organization to organization. Especially, Regulation and Policy Contents may not be up to date with the latest amendments from the legislature, and policies listed are generic. These may have to be customized by your Legal Team as it's written in response to the Regulation. This book is not intended to convey, does not include, and should not be relied on as legal advice.
How this Book is Organized
This book consists of five chapters, each of which focuses on a topic related to the GDPR and the approach your organization should consider taking to deal with it. Chapter 5 has a proper use case which the Business user should check out. Here’s a glimpse:
- Chapter 1: ‘How to Adopt GDPR’: What is GDPR anyway, who does it affect, and how? What does it require, who’s overseeing it, who can help? And, is there perhaps a silver lining?
- Chapter 2: ‘Insights into What Data is Affected’: All kinds of different data types exist out there, some that fall under the watchful eye of the GDPR and some that don’t. How can you tell the difference, and what kind of governance will help you deal with the challenge?
- Chapter 3: ‘Discovering the Data’: The larger your organization, the more places in-scope data may be stored (or hiding). You need to find all the in-scope data, assess the risks each data store poses, and figure out how to minimize those risks.
- Chapter 4: ’Manage Risk and Compliance’: GDPR governs what you can and cannot do with the data you have gathered. But it also underscores the need to keep prying eyes from gaining access to data they should not see. How can you gain the required control?
- Chapter 5: ‘Accelerate GDPR Journey’: The GDPR Accelerator has prefilled templates with sample data to showcase how “Sensitive Data” moves across the Onboarding Process. Each template defines the facets and relationships between the facets. It’s mainly concentrated on importing the GDPR body and polices related to the GDPR. Facets that are targeted for this accelerator are Glossary, Regulation, Policy, System, Datasets, Attributes, People, etc.
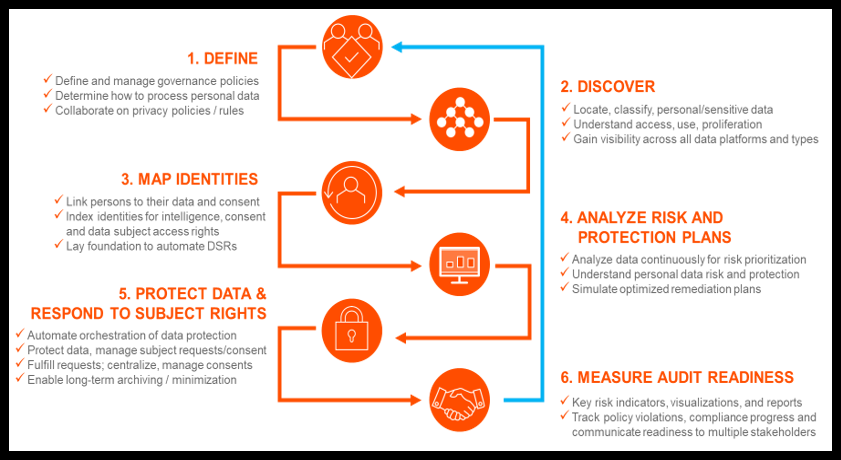
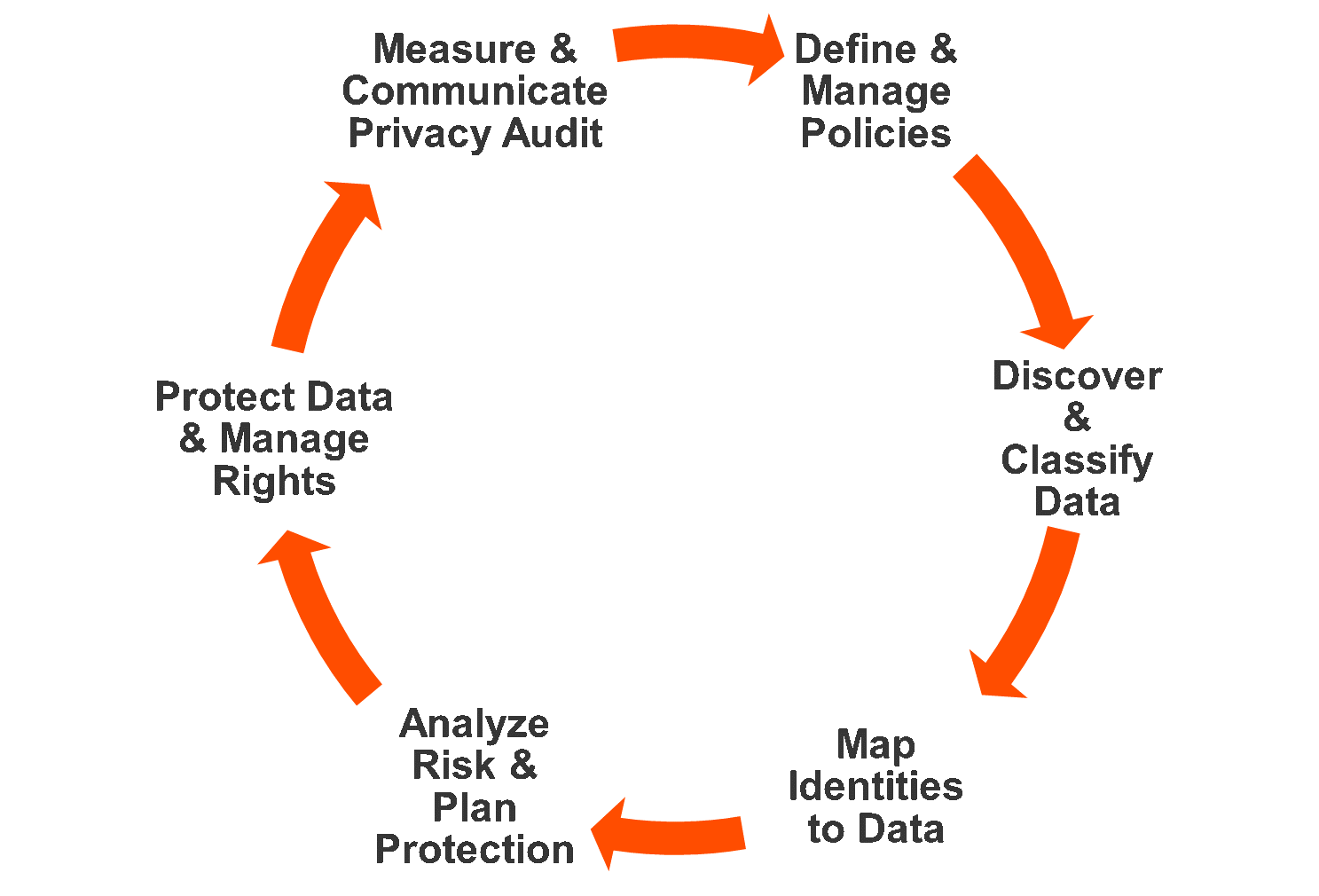
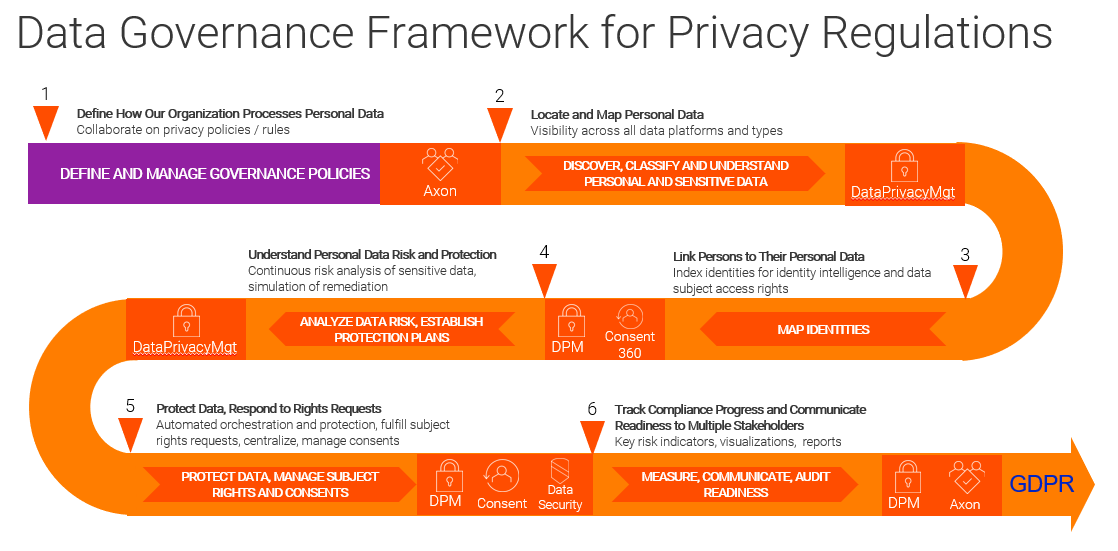
The below framework helps the organization with where to start, what are all the considerations to be in place, and how to move ahead. Leverage Informatica Data Privacy Framework - A continuous journey to scale privacy governance and reduce risk!
Figure 1. Informatica Data Privacy Network
What is GDPR?
GDPR is a regulation that requires businesses to protect the personal data and privacy of individuals in EU member states. And non-compliance could cost companies dearly.
Companies that collect, store, or use data on individuals in the European Union (EU) countries need to comply with strict new rules around protecting customer data. The General Data Protection Regulation (GDPR) sets a new standard for consumer rights regarding their data.
Whom it affects, and How?
The GDPR defines several roles with responsibility for ensuring compliance, including the Data Controller, the Data Processor and the Data Protection Officer (DPO). The Data Controller defines how personal data is processed and the purposes for which it is processed. The Controller is also responsible for making sure that outside contractors who process personal data on the controller’s behalf do so in compliance with the GDPR.
Data Processors are the outside contractors or other entities that process personal data on behalf of the controller. The GDPR holds processors liable for damages caused by the processors’ non-compliance with the GDPR or with the controller’s instructions. Where a processor such as a cloud provider fails to pay, however, the controller is ultimately responsible for the entire damages, even if the fault is entirely on the processing partner.
The GDPR requires the controller and the processor to designate a DPO to monitor GDPR compliance and advise on obligations under the GDPR. Companies are required to have a DPO if they are a public authority other than a court, perform regular and systematic monitoring of individuals on a large scale, or process on a large scale special categories of personal data or personal data relating to criminal offenses and convictions.
Rights and responsibilities under GDPR:
- Individuals have the right to be informed about the collection and use of their data. This is a key transparency requirement under the GDPR.
- You must provide individuals with information including your purposes for processing their data, your retention period for that personal data, and who it will be shared with. We call this ‘privacy information’.
- You must provide privacy information to individuals at the time you collect their data from them.
- If you obtain personal data from other sources, you must provide individuals with privacy information within a reasonable period of obtaining the data and no later than one month.
- The information you provide to people must be concise, transparent, intelligible, easily accessible, and it must use clear and plain language.
- It is often most effective to provide privacy information to people using a combination of different techniques including layering, dashboards, and just-in-time notices.
- You must regularly review, and where necessary, update your privacy information. You must bring any new uses of an individual’s data to their attention before you start the processing.
- Getting the right to be informed correctly can help you to comply with other aspects of the GDPR and build trust with people but getting it wrong can leave you open to fines and lead to reputational damage.
Challenges of Compliance:
- Many new requirements - To encourage transparency, various obligations regulate information, access, and communication with the data subject. New and improved rights for the data subject, such as the right to data portability and the right to be forgotten, impact companies because such rights need to be accommodated in their internal processes.
- Very process-driven - The GDPR sets out specific processes for companies to adopt. It intends to help the company structure and formalize certain subject areas like risk assessment and decision making. By putting these structured processes
- Very tangible and visible/verifiable functions and steps need to be realized - It’s not only a question of complying with general principles, such as data minimization or accuracy; the GDPR also imposes very concrete measures. For instance, the GDPR imposes an obligation on companies to keep internal records of their data processing activities. Also, data breaches must be notified to supervisory authorities without undue delay unless unlikely to result in a risk to the rights and freedoms of individuals and it also must be documented, explaining the underlying facts, the likely consequences, and the remedial action that is taken. And there is more: new roles will be created, such as the Data Protection Officer (DPO). Appointing a DPO can be mandatory as explained above, for example for businesses engaging in profiling or tracking online behavior on a large scale or for biomedical companies that process health data on a large scale.
- Increased fines and sanctions - The GDPR could have a huge impact on companies failing to comply. The supervisory authorities can take one or more measures listed in the GDPR, such as (i) issue a warning or impose a temporary or definitive ban on processing personal data, or (ii) impose a fine up to EUR 20,000,000 or 4% of the total worldwide turnover, depending on the circumstances of each case, or both.
The GDPR is Europe's current data protection regulation. It replaced the previous 1995 data protection directive. The new regulation started on 25 May 2018. It is enforced by each member state’s supervisory authority(ies) (the Information Commissioner's Office (ICO) in the UK).
One of the biggest, and most talked about, elements of the GDPR is the power for regulators to fine businesses that don't comply with it. These monetary penalties will be decided upon by the supervisory authority. However, the GDPR is not ultimately about fines. It’s about putting the consumer and citizen first.
You could argue that advances in technology are among the root causes of the many issues that the GDPR addresses. The more dependent we become upon data and the technology used to collect, process, and share that data, the more we need to protect data and to ensure that it is not used in ways contrary to the interests of the individual.
The good news is that technology provides solutions, too. In fact, with every challenge comes a new opportunity, and the improvements in understanding, governing, and overseeing data necessary to meet the challenge of GDPR can also result in additional benefits around your organization’s use of data.
Technology providers have stepped up to make it easier to address GDPR requirements. Informatica brings deep expertise in data management and data governance to help organizations on their path to GDPR compliance. Innovative new data management capabilities make it possible for you to wind up in a better spot after GDPR than you were in before. Informatica has developed integrated and intelligent software solutions for governance and compliance that provide an ideal support system for a GDPR initiative.
Figure 2. Shared Metadata-driven Intelligence Accelerates Your Privacy Journey
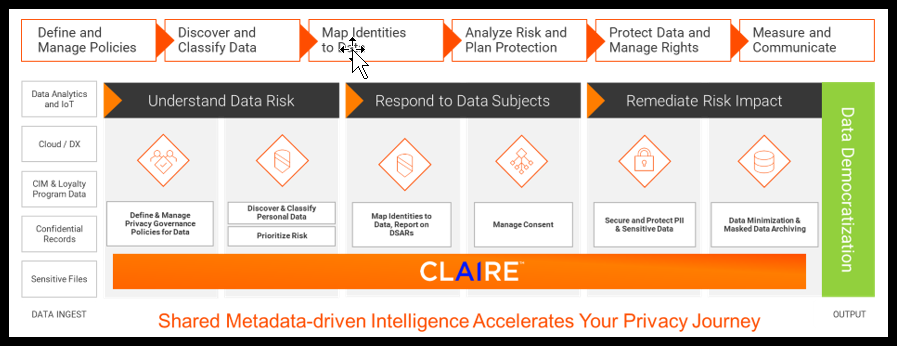
Every industry is affected by the digital transformation that has upended the way business is done, as well as the growing amount of data that is collected, processed, and shared. Quite a bit of that data can be attributed to specific individuals, or what the GDPR views as data subjects.
The more data your organization deals with, the more challenging it becomes to figure out ownership, control, and management of any given bit of data. You may know of the risks in some cases, but the fact is that there is a lot of risk in what you don’t know, too. If your initiative is going to be as successful as possible, you want an enterprise-wide approach to data governance.
What Falls under GDPR
Personal data falls under GDPR. Some examples of personal data are:
- Name
- Address
- Telephone
- Credit Card
- SSN
- Account Data
- Customer Info
- Biometric Data
- Racial or Ethnic Data
- Political Opinions
- Sexual Orientation
- In many cases, web data such as location, IP address, cookie data, and RFID tags
- Health and Generic Data
The Geographic Scope of GDPR
Unlike under the current regime, the GDPR places any business located anywhere in the world under its terms if the business offers goods or services to people in the EU or monitors the behavior of EU individuals, irrespective of whether it has a presence in Europe.
Taking an Enterprise-Wide Approach
Today it is more important than ever for marketing, technology, and legal teams to work together to focus on a cohesive result rather than crossing the departments’ independent “finish lines.” As organizations cast a wider global net in marketing, they need to get their legal teams more involved because there are jurisdictional and legal compliance issues that arise from advertising globally.
No matter where your company is located, if it has an online presence, it will likely be affected by GDPR. Because the regulation aims to ensure that users know, understand, and where applicable consent to private data being collected about them. Companies are now required to be clear and concise about their collection and use of personal data. Companies have to spell out why the data is being collected and whether it will be used to create profiles of people’s actions and habits. Moreover, consumers will gain the right to access data companies’ stores about them and the right to correct inaccurate information.
Technology and Business go hand in hand:
- Policy Definition: This includes business and IT definitions, plus documentation across all operational levels of the business, and logical and physical data and process models.
- Responsibilities: You must determine who owns the data, who uses the data, and what functions within your organization have responsibility for the data’s quality and security.
- Definition of terms and process: This has to do with business processes, key data entities, attributes, systems, quality and controls, standardization, and how the business captures and acknowledges the consent of data subjects to use their data.
- Change process: You need a governed process for definitions, a governed process for change, and overall process governance.
- Linkage to artifacts: This refers to logical-to-physical artifact linkage, producing the technical and business data lineage needed to understand the dependencies, and ensure the quality, of in-scope data.
Your Data Governance Initiative
Data Platform should deliver a single source of truth for data governance and regulatory compliance.
- Powerful MetaData: Metadata turns unstructured data into objects that can be separated into the useless, the useful and the mission-critical. It’s a crucial tool for efficient long-term data management.
- Automated Enrichment: We shine a light on dark data assets, enriching them with valuable metadata to help simplify compliance and secure your data, no matter where it resides.
- Simplified Compliance: Our intelligent data governance solutions are included on a single platform that extends across private and public cloud, reducing the cost and complexity of data governance and compliance reporting.
Different ways in which Data is siloed across an Organization:
- Company Culture: Often departments are siloed from each other, especially in larger companies. Sometimes this occurs because there is internal competition, but often it happens because one department sees itself as separate from another and doesn’t consider where information should be shared.
- Organizational Structures: Unless an organization specifically works to integrate different departments, it’s easy to build layers of hierarchy and management that deter departments from sharing information.
- Technology: It’s not uncommon for different departments to use different technology, making it difficult for the departments to share common information. For example, maybe the Sales team uses Salesforce, but the Marketing team doesn’t have this tool. Yet, it might contain valuable information that the Marketing team could use. An IT survey showed that most companies have between 1-200 applications for their different departments. Consider how unwieldy it can be to find information when you have so many different sources.
- Inability to get a comprehensive view of Data: If your data is siloed, relevant connections between siloed data can easily be missed. Suppose, for example, the Marketing team has excellent data on which Marketing campaigns attracted a lot of attention in a geography, whereas the Sales team has information about sales in that same geography. What if you could bring that information together? Imagine how much clearer the relationship between Marketing campaigns and sales would be.
- Wasted Resources: Consider what happens if you have a database with customer information for the Marketing team and a separate one for the Sales team. Much data is duplicated between these departments. It costs money to store all this data, and the more data a company stores, the less the organization can spend on other requirements
- Inconsistent Data: In Data Silos, it’s common to store the same information in different places. When this happens, there is a high chance that you will introduce data inconsistencies. You might update a customer address in one place and not another. Or, you might introduce a typo in one set of information. When the data is in one place, you have a much better chance of maintaining the correct information.
Typically, sensitive information is scattered across the enterprise. Over the years, the data center can grow to include potentially hundreds or thousands of database servers that store this sensitive information. These servers can be scattered across the globe. Developers and quality assurance testers who create their databases with sensitive information compound this situation and most companies simply do not know where all their data is. This lack of visibility into critical data assets leaves companies exposed to significant risks. The ability to understand where data stores are located, what is in those stores, and who has access to stored data is a critical step in understanding data risk and achieving data governance and compliance.
Risk management requires knowledge about data assets- where they are, what is happening to them, what bad things might happen to them, and, most importantly, the costs associated with the bad things that could happen to them.
Organizations must control three key areas of data risk:
- Discover sensitive data: Discovery begins with finding and identifying critical data assets in the network, determining what data stores exist, and finding information inside of those data stores.
- Assess data activity risk: To understand data risk an organization must know who has access to which data. Visibility into data usage and the associated risks is essential for developing the appropriate compliance and security strategy. This includes identifying how data is being used and which users and applications are accessing data from where and when. This assessment must encompass all applications, users, and processes relating to the access to sensitive data.
- Ensure data compliance: To comply with a variety of privacy and financial regulations, dozens of data protection requirements must be addressed. Compliance with these regulations includes the ability to provide regular and detailed reports that address the requirements of outside assessors and internal stakeholders.
Capabilities of Intelligent Data Catalog:
- Data Policy Definition: This capability gets into both business and IT definitions, as well as vague data and policy conflict.
- Automated Data Discovery: This capability is about finding relevant in-scope sensitive or personal data on the first pass, followed by continual monitoring, plus classification of data and integration of supporting systems. Data must be definedin context, with intelligent policies that identify whether a combination of specific data elements (such as name, email,and national ID) can be combined in any data store to identify privacy data of GDPR subjects.
- Data Proliferation Analysis: Data tends to move around, which is what proliferation refers to. It isn’t only a matter of finding out where the data is. You need to know where it goes and what new sources of data are emerging.
- Data Risk Scoring: This considers the factors listed earlier, including movement of data, proliferation, access, volume, value, and prioritization. This capability should include planning, history, and score monitoring over time.Monitoring would include excess access, anomalous user behavior, and cross-border data transfers.
Introduction:
Complying with GDPR may require a lot of processes and procedures as you ensure that you can answer data subjects’ requests and implement their rights. There’s also a fair amount of technology because all the sensitive data involved must be secure.
Security is certainly a technological matter, in terms of building defenses against hacking. But in the end, much of it is a matter of creating controls to ensure that only the right people can access sensitive or personal data.
This chapter focuses on the need for properly restricting access to the data you’re holding on protected individuals. It describes helpful data protection controls and outlines technology solutions.
Why Data Protection Controls
Of the requirements of the GDPR, one of the most basic tenets is protecting your data from being accessed by unauthorized users. That calls for some serious data security controls.
To begin with, from an IT perspective, you face various requirements that privacy data be encrypted, access-controlled, removed, masked, or pseudonymized. It covers data being used in a wide variety of ways, from internal processes, customer services, and order processing to analytics and reporting. Your concerns about data protection also cover data related to testing and development, activities that bring their own sets of issues and challenges.
In practice, ensuring effective data security means reviewing for compliance purposes all the applications that contain or access personal data. These applications need tight data access control for personal data at a user level.
Consider production data - Various people might have access to the data, from administration to product support to app users to partners. Some are authorized, but some are not, and the app infrastructure must remain as is. Because you have unauthorized users in the mix, you would want to mask sensitive or personal data to prevent unauthorized access, through what’s known as hand, involves interactions with data analysts, data scientists, and testers and developers, and potentially no one is an authorized user. Your goal is to remove any risk of sensitive or personal data access, so an effective approach is to fictionalize data for testing or research purposes and permanently change sensitive or personal data. Persistent data masking is the name of the game.
How you’ll protect your organization’s data and ensure that you have the appropriate controls? How do you gain the kind of access control you need to protect the in-scope information of data subjects? By enabling strong and sophisticated security controls. Your chief legal officer, CIO, and chief data officer should be part of the solution concerning this dilemma. As for the required capabilities, you need enterprise-wide protection and controls over data. These data controls must cover access controls, data deletion and retention, data masking, archiving, and pseudonymization.
The below technology helps with protection:
- Risk analysis input: You’ve done the risk scoring; now use it to direct data control methods.
- Orchestration: This musical term refers to the ability to schedule and coordinate data protection tasks by identifying risks and ongoing monitoring of unsafe access or conditions.
- Data security controls: These include static or dynamic masking, pseudonymization, role-based access controls, encryption, and tokenization.
- Change/update history: You’re comparing the application against source systems, the record masking or archiving outcomes against a consent record, and generating an audit trail for evidence.
- Archiving: This activity takes data out of production systems and archives it, logs the activity to provide evidence, andmoves sensitive or personal data offline to prevent accidental usage or access.
Informatica weighs in with powerful solutions that help with privacy and the security of data assets. You can use Persistent Data Masking and Dynamic Data Masking to help automatically limit the number of people and systems that have unrestricted access to personal data. Informatica’s Data Privacy Managementmeanwhile, provides extensions to Persistent Data Masking for protection. Data Archive helps organizations remove data that is no longer needed for business operations but could pose privacy risk if exposed. It also helps support the data minimization principles outlined in the GDPR.
It’s tremendously helpful to build this kind of automation into data masking. You reduce the risk of personal data breaches and make it a whole lot less likely that unprotected personal data finds its way out to an accessible environment.
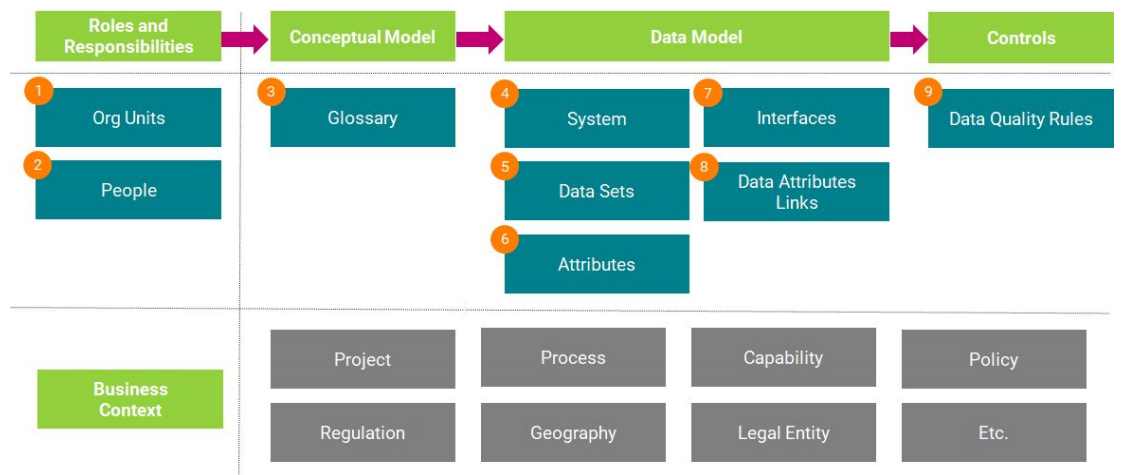
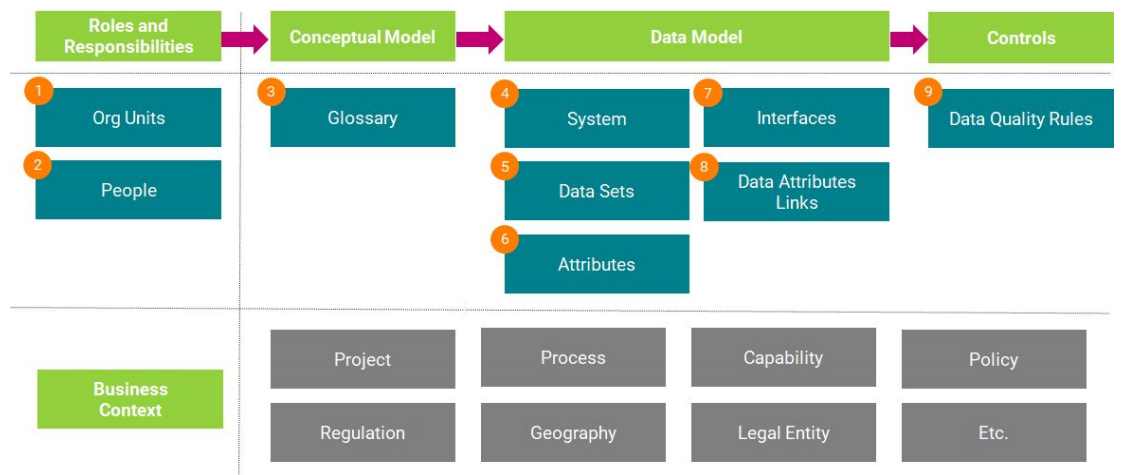
The GDPR Accelerator has the prefilled templates with a sample of data mainly to showcase how the “Sensitive Data” moves across the Onboarding Process. Each template defines the facets and relationships between the facets. Mainly concentrated on importing the GDPR body and polices related to the GDPR. Facets that are targeted for this accelerator are Glossary, Regulation, Policy, System, Datasets, Attributes, People, Role, Process, Legal Entity OrgUnit, and Data quality as well.
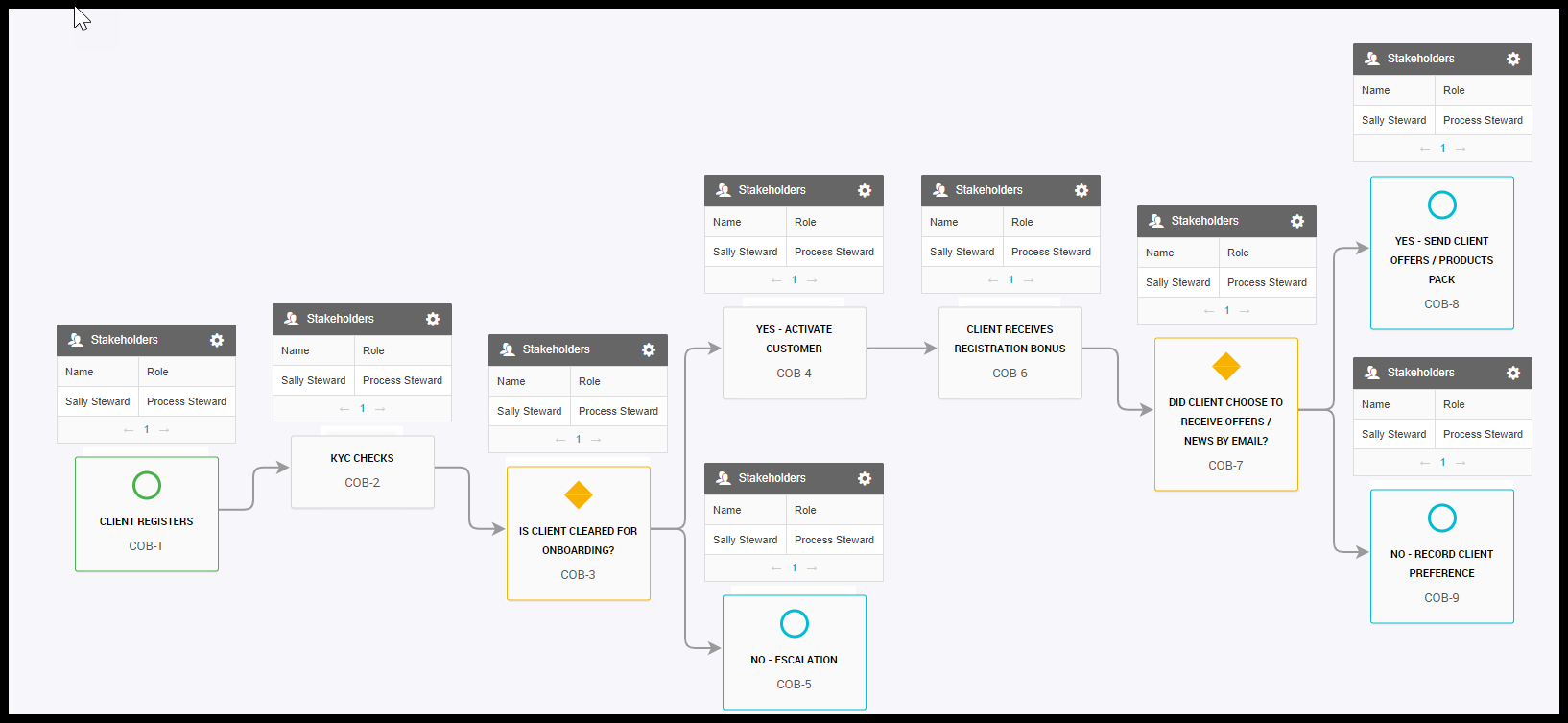
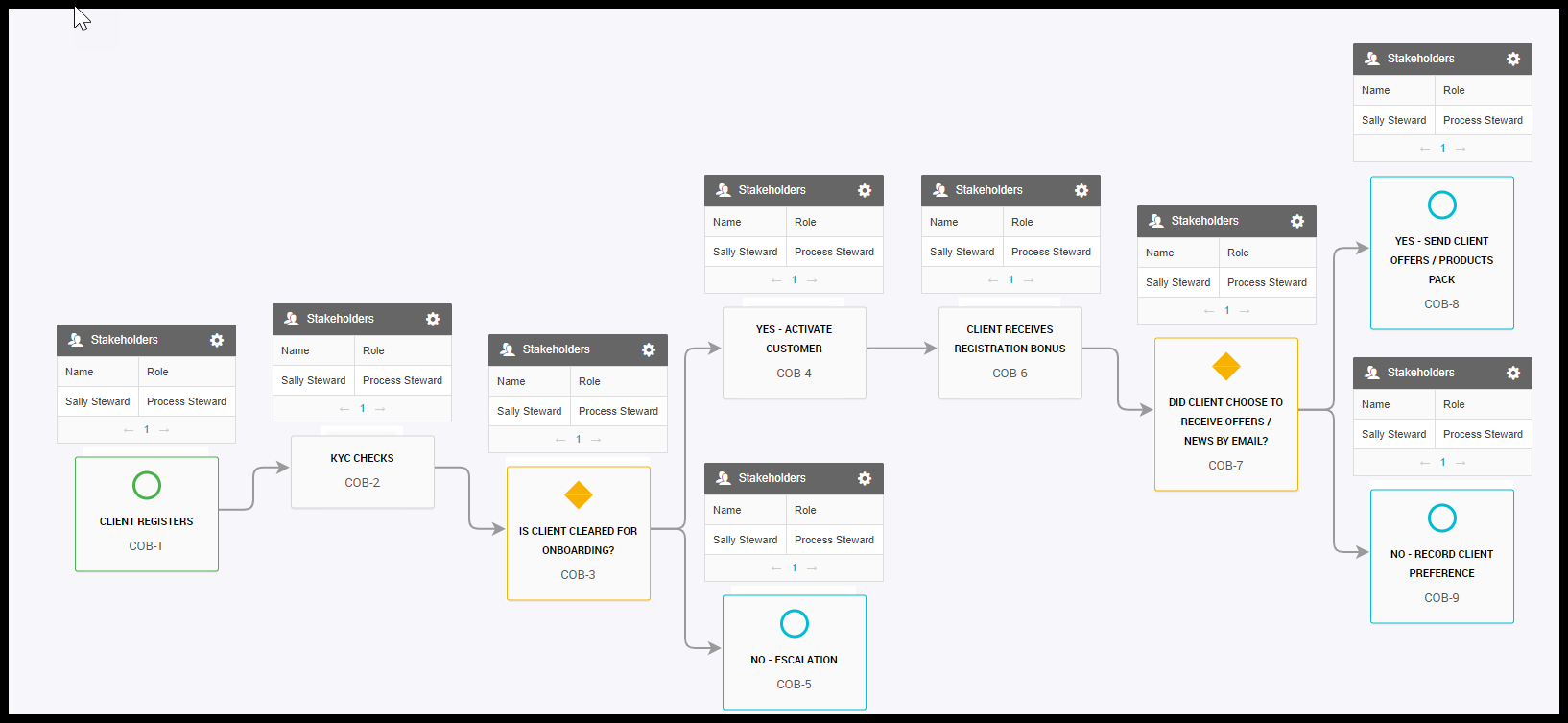
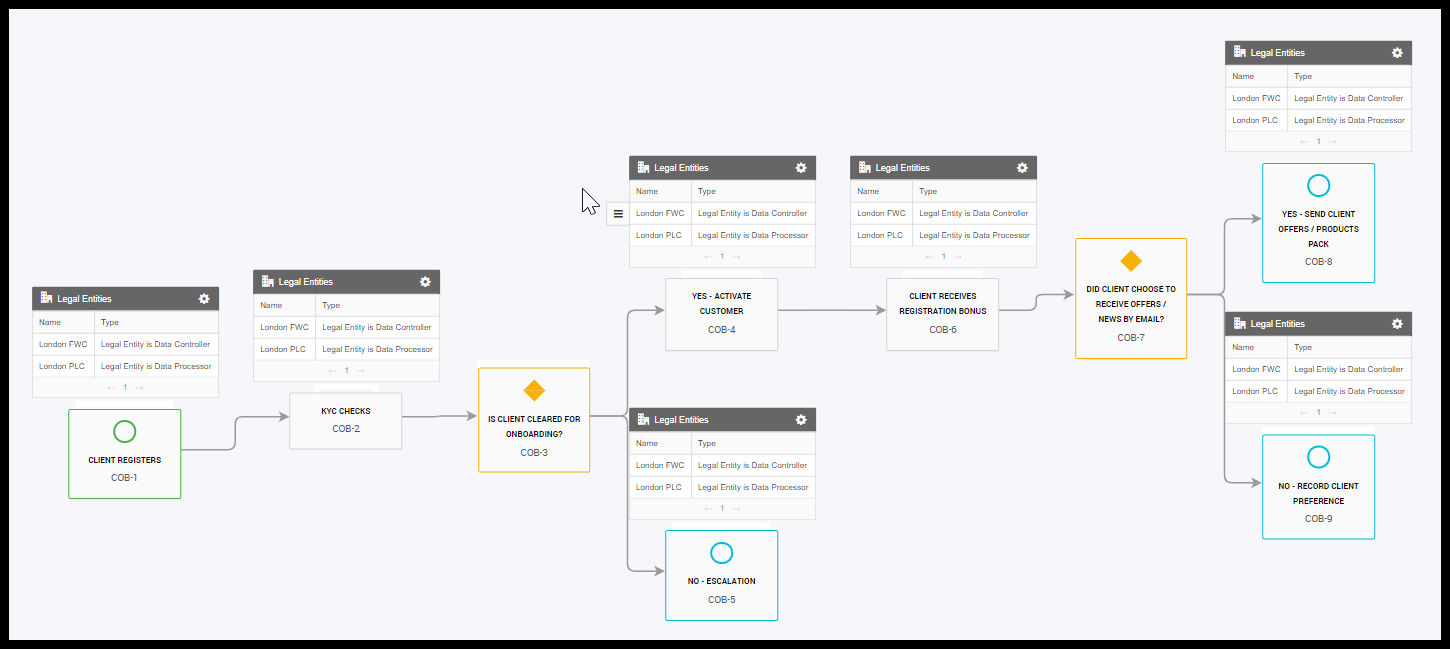
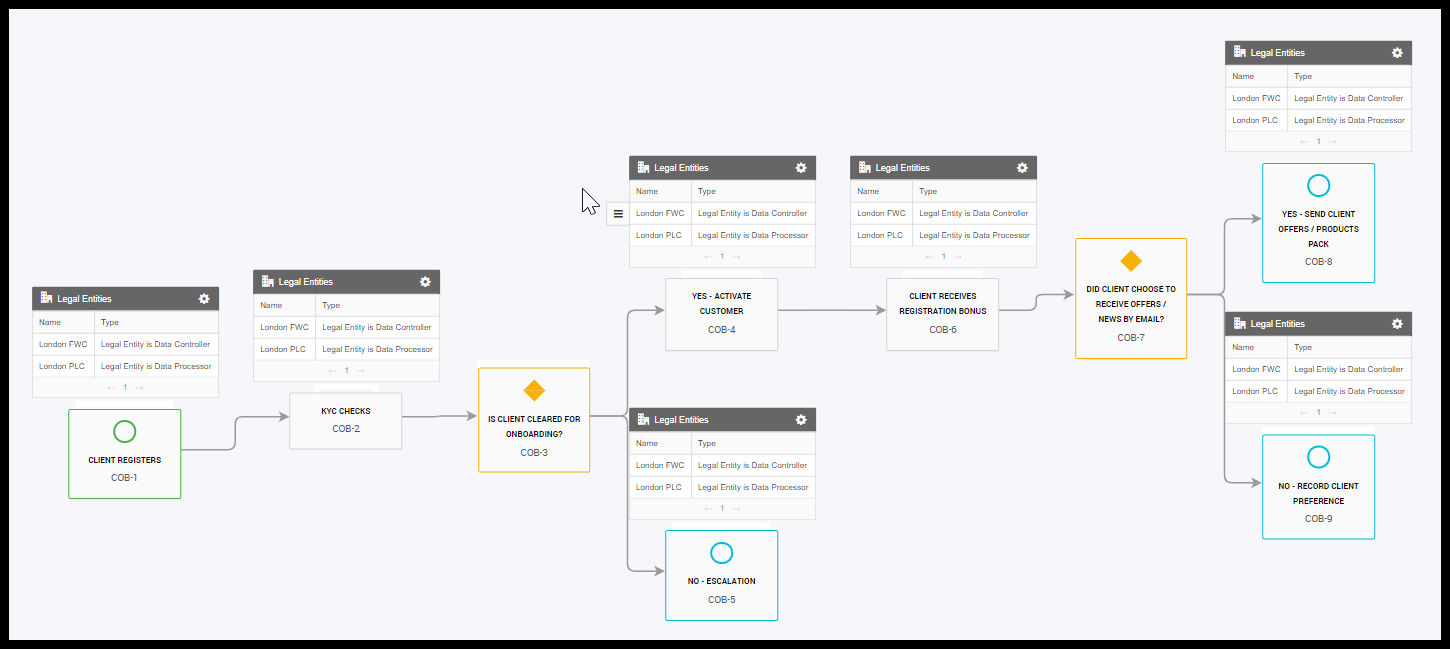
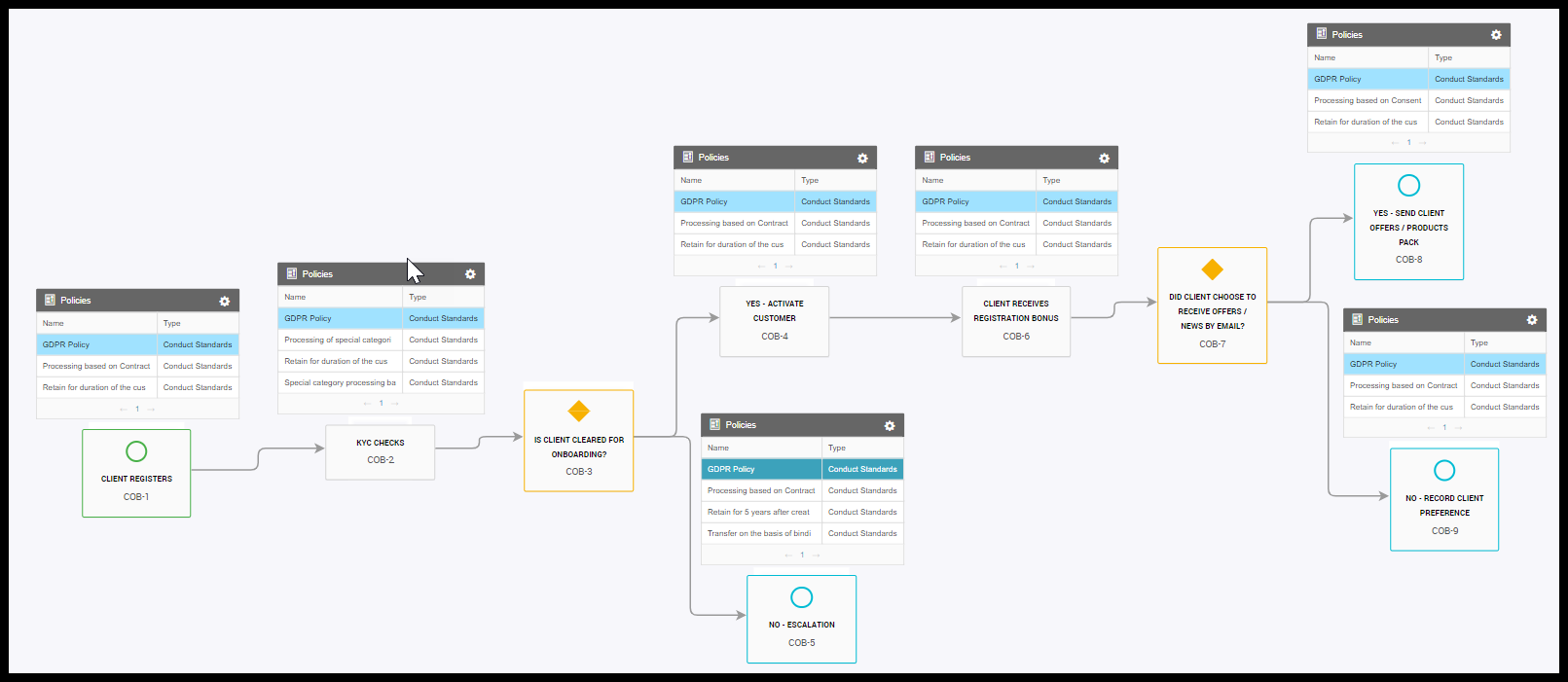
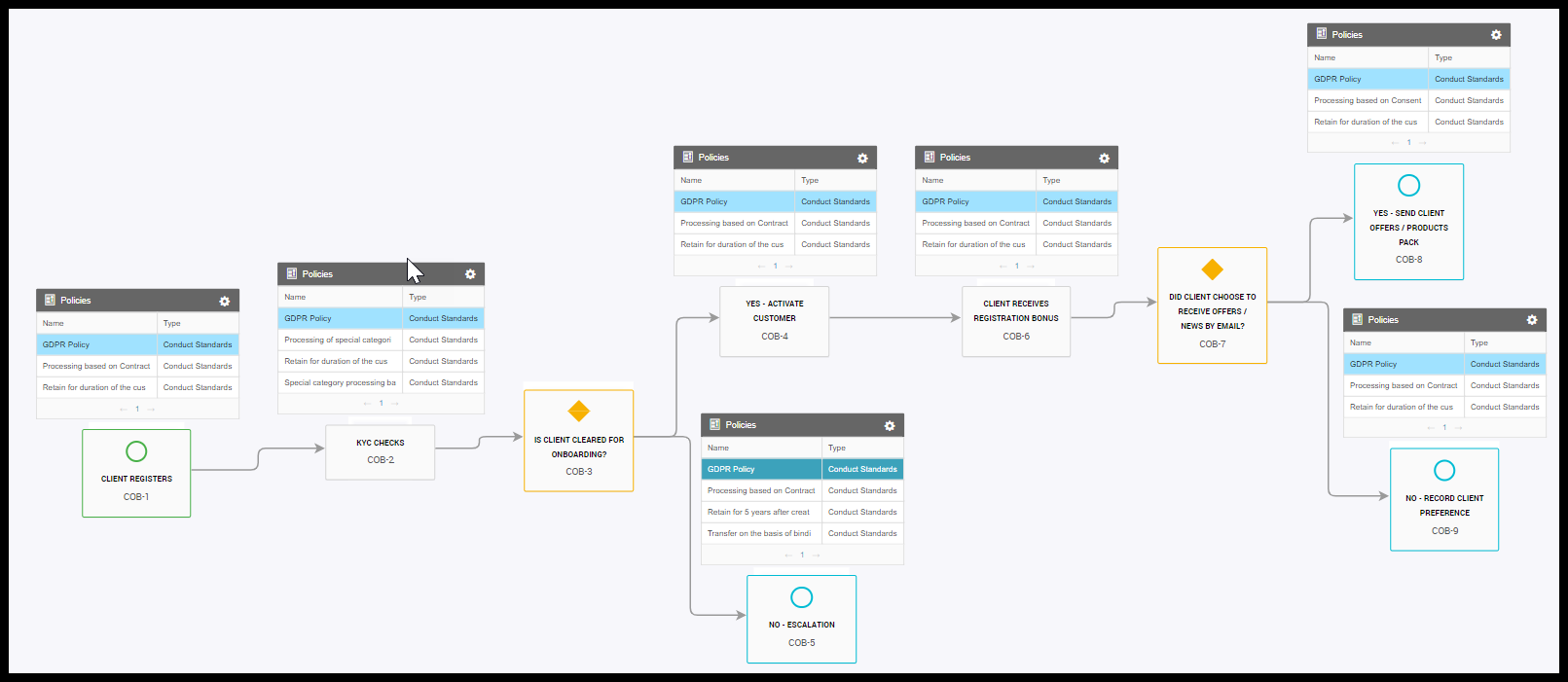
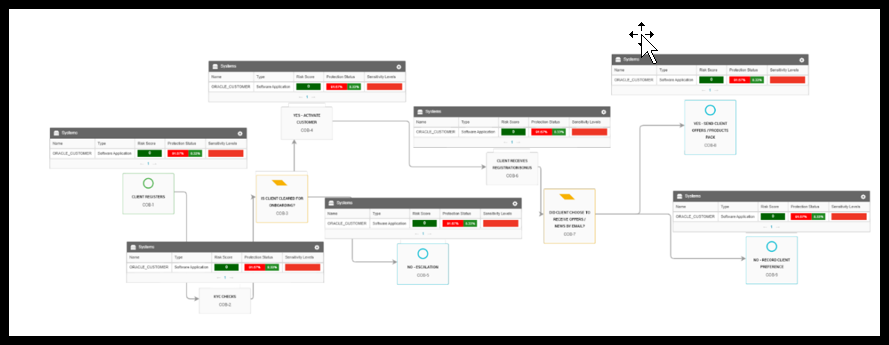
Templates for different facets like glossary, regulation, Policy, people, system, Datasets are straight forward. These templates import the respective sample data to each facet. The other set of templates builds a relationship between the facets and adds the stakeholders responsible for the asset. About the process: The template has another subprocess which helps to build a proper Onboarding process example like Client registration, KYC check, and so on. Process templates have the capability of attaching another subprocess as well.
After the complete import of the templates, the Onboarding process example takes you to the demopart of how sensitive data moves across the entire process. Overlays in the process facets show:
- Related Glossaries
- Affecting Systems
- Responsible Stakeholders
- Legal Entity processer and contributors
- Related Policies
- Data Quality results
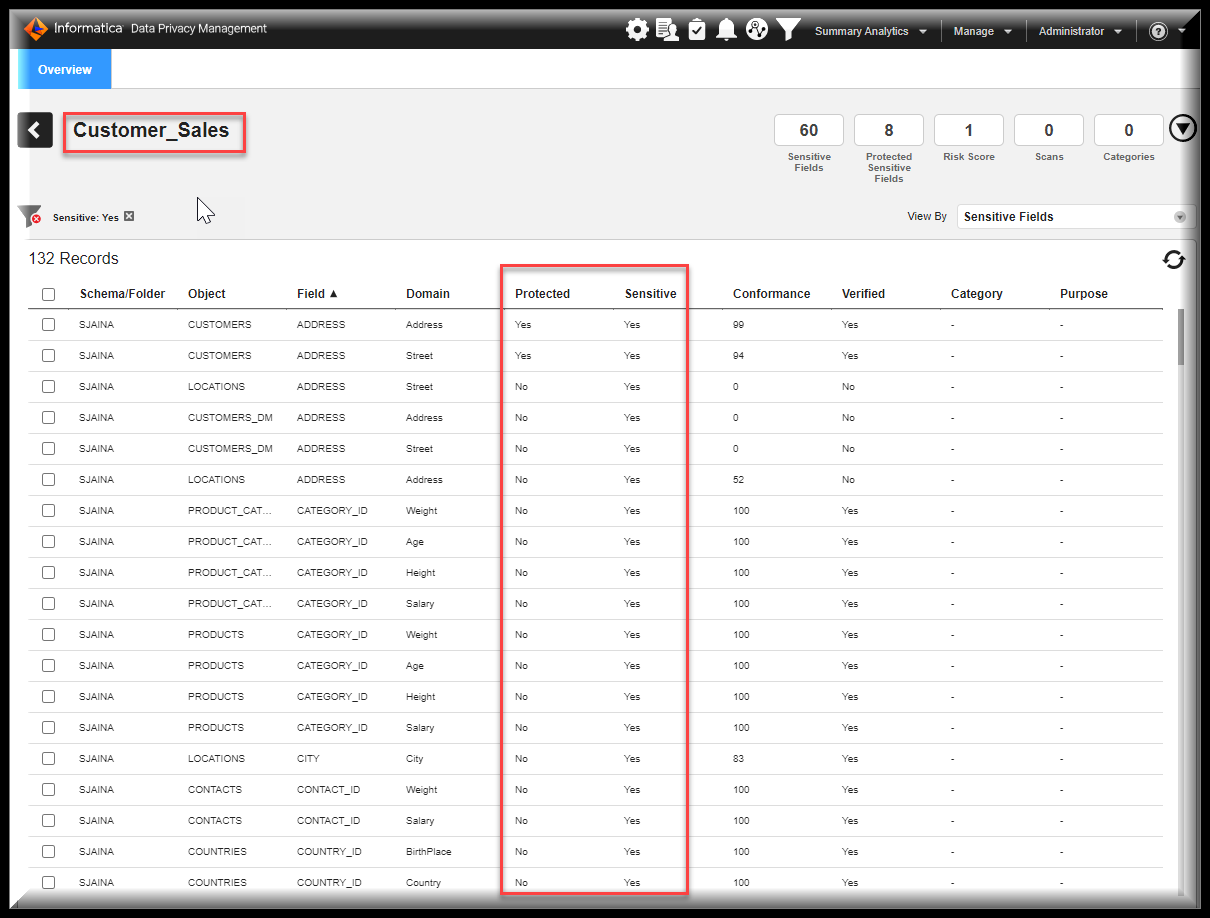
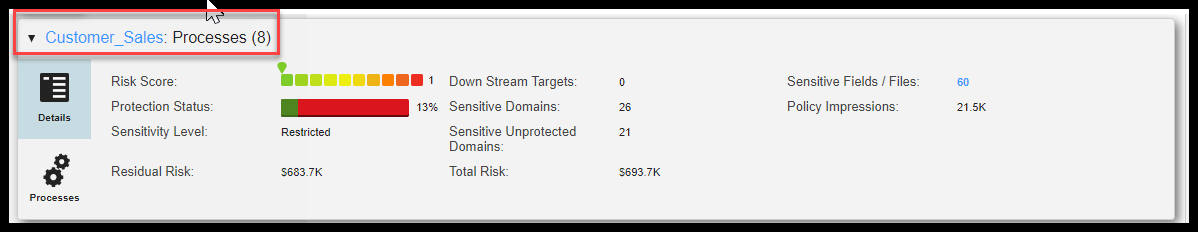
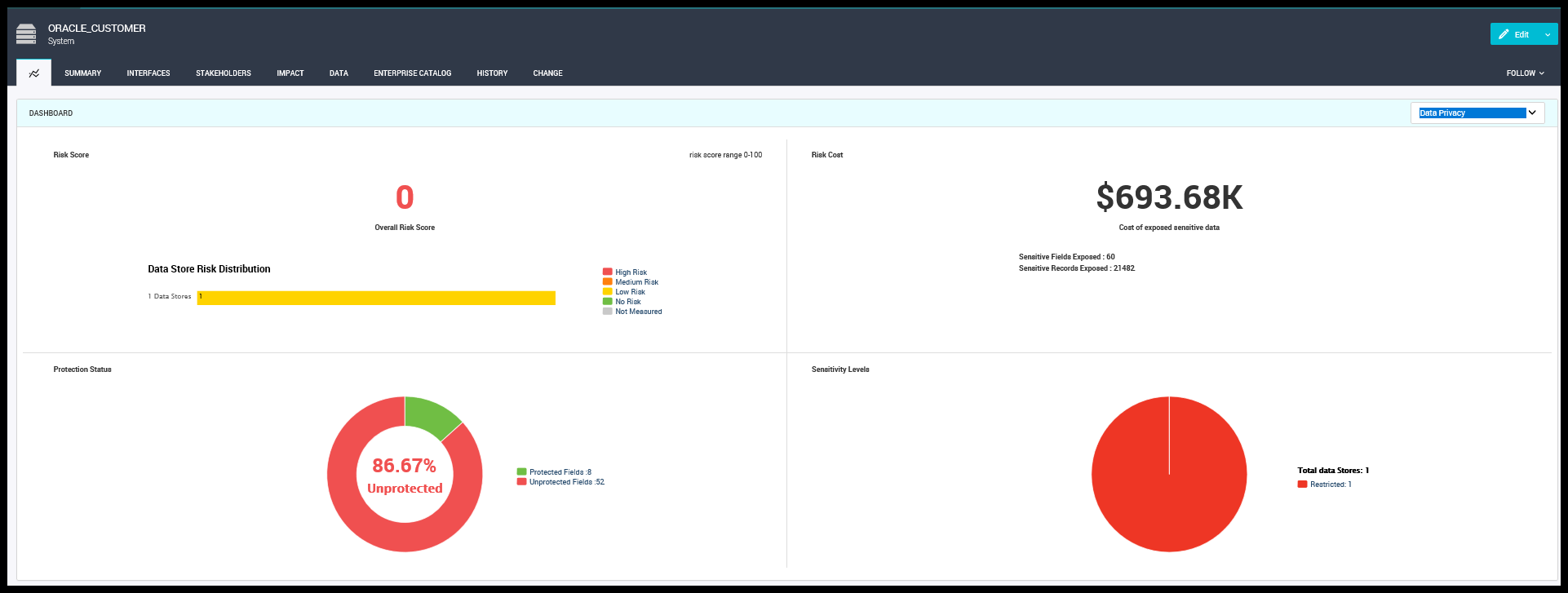
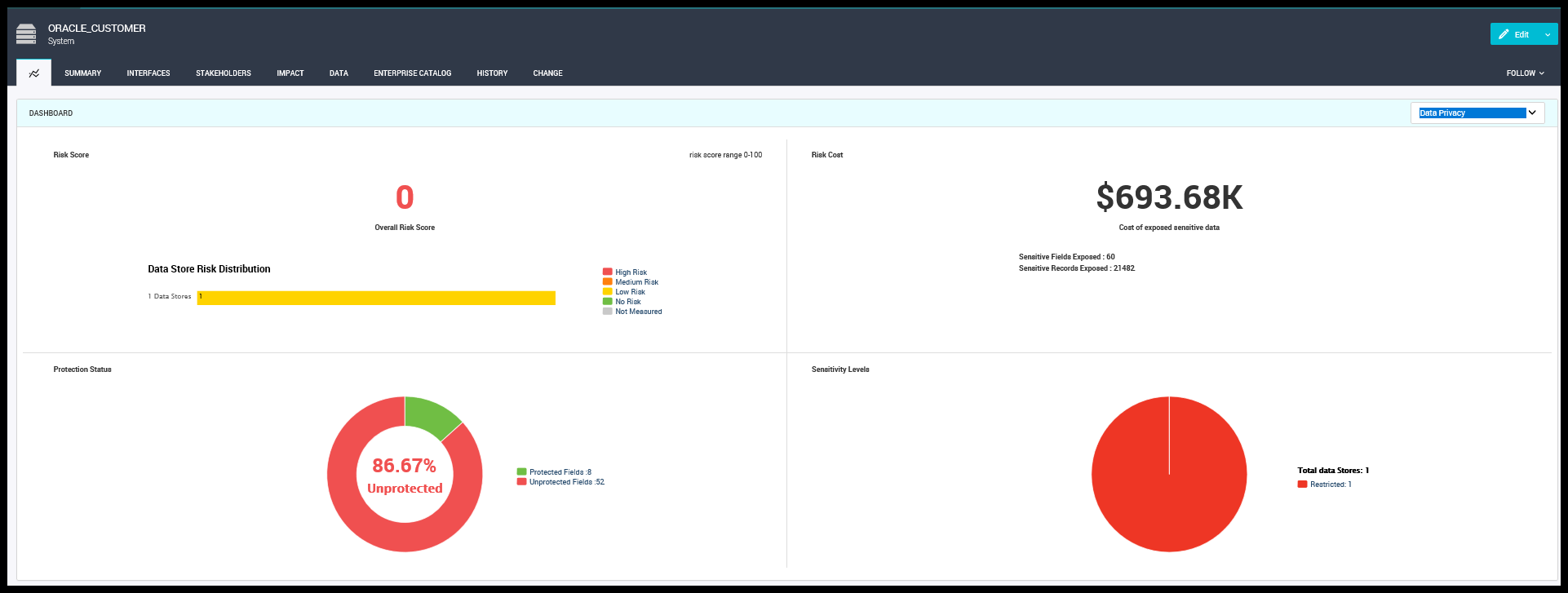
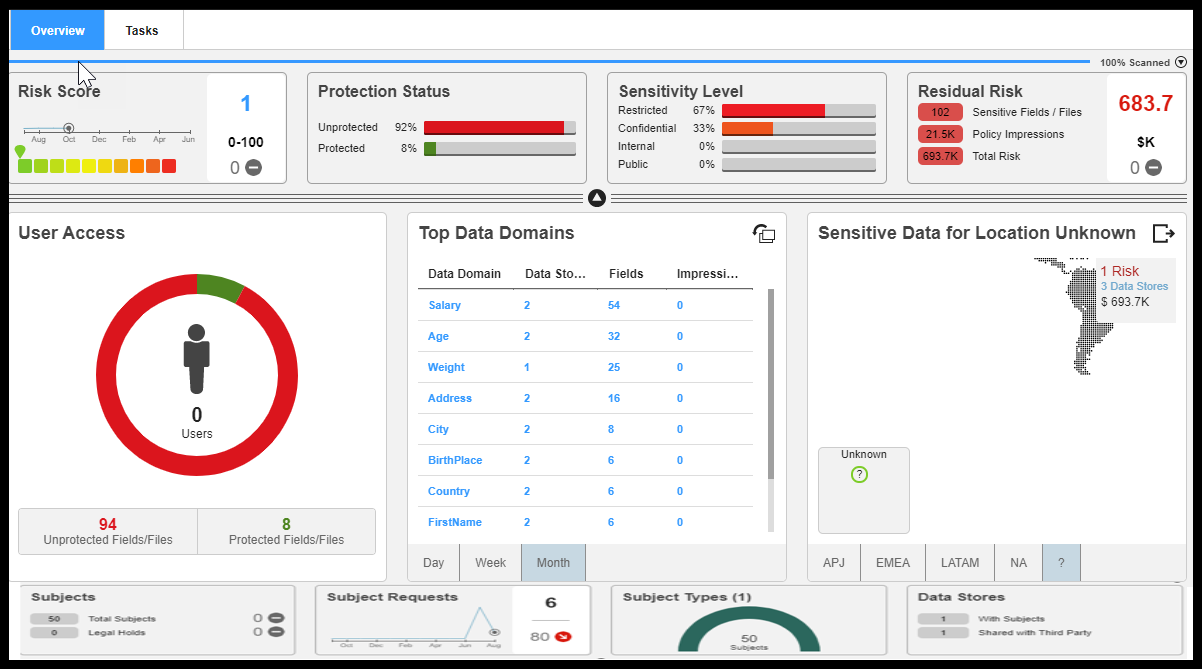
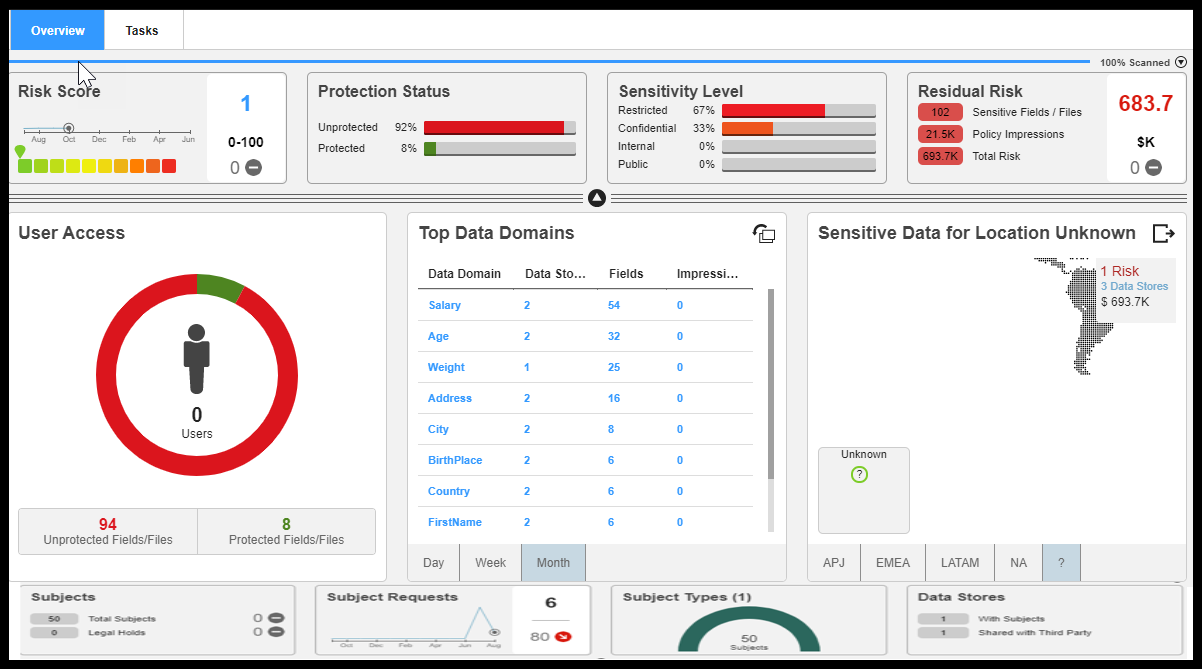
Along with this sample process example, there will be an exercise with another tool called “Data Privacy Management” that helps an organization to check whether the sensitive data is Protected, the Risk score, Risk Cost, and Security Levels of the Datastore. The tool has the capability of masking sensitive data with the privacy rules applied. With the help of a privacy dashboard showing to the Business users in Axon, it makes users immediately take actions based on the result. The Risk Score, Protection status, and Sensitive Levels are visible at the process overlays for System.
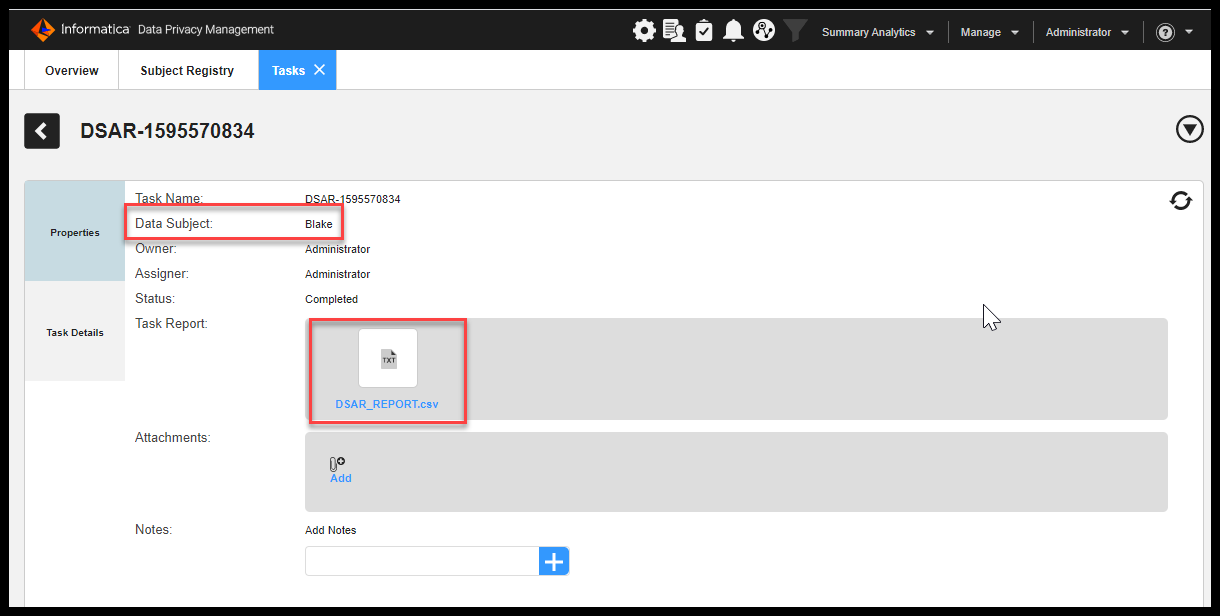
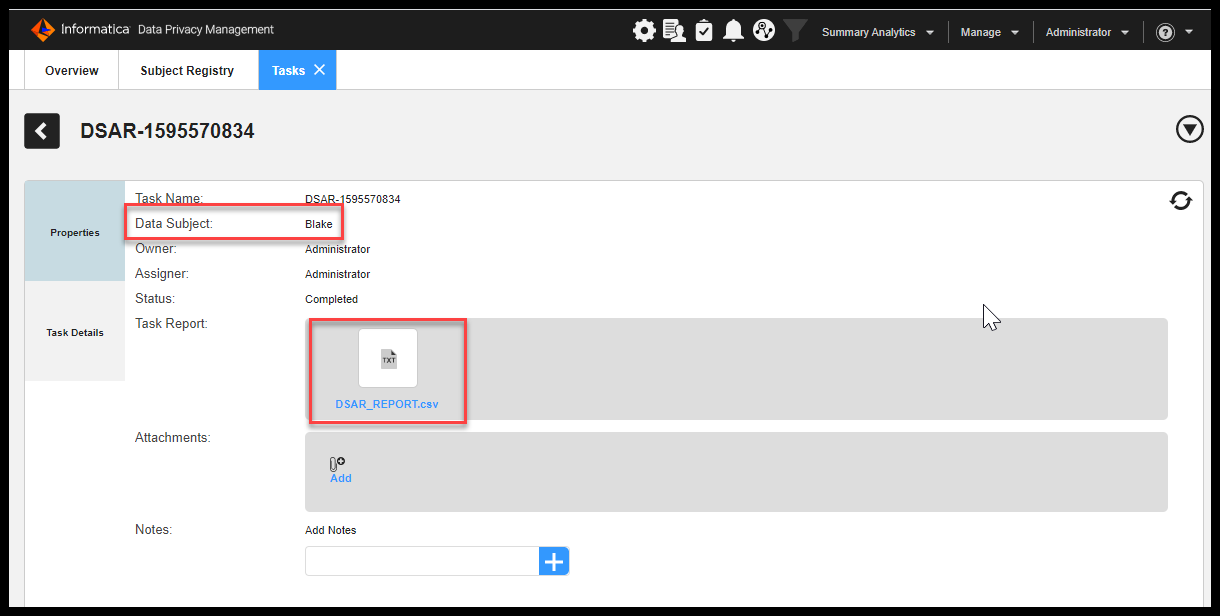
The DSAR reports can be generated with the help of DPM and a sample report is given in this accelerator. To Generate the DSAR one must create the Subject registry for the resource and the sample files required to generate the Subject Registry are included in the Accelerator.
There could be a scenario where Business users want to understand the sensitive data which are related to any groups say GDPR/PII/PCI domains and can see the holistic view
on a single page. A view is showed in this Accelerator to show how the table is linked to data domains, a business term, rules, profile results, a user associated, and so on.
The other requirement would be change management, this would be the main use case requirement in most organizations that see the audit reports on what all have changed, who have made changes, who have requested, and so forth.
Herewith this Accelerator we do have a workflow that the user can customize and can build workflow as per the required basis.
Workflow is utilized and showed during the journey which talks about the roles responsible for each task and audit is maintained for the same to monitor.
The Accelerator covers the main use cases like:
- SRR (Subject Rights Requests)
- DSAR (Data Subject Access Request)
- RTBF (Right to Be Forgotten)
- Right to Rectification
Configuration Video
Loading Assets - Object Dependencies
DonBank Inc. is one of the largest banking and financial services organizations in the world. DonBank’s International Network comprises of around 6,000 offices in over 75 countries and territories in Europe, the Asia-Pacific region, the Americas, the Middle East and Africa.
DonBank Inc. is one of the three major clearing banks in Europe and is a wholly owned subsidiary of DonBank Holdings. The business ranges from the traditional high street roles of personal finance and commercial banking, to private banking, consumer finance as well as corporate and investment banking. Across all brands the bank operates in some 1800 sites in the Europe.
The DonBank has its head office in Utrecht, Netherlands. DonBank is a data driven organization. It is focused on implementing GDPR.
The role of the Data Protection Officer in DonBank is an enterprise security leadership role and is required by the General Data Protection Regulation (GDPR). As a DPO he is responsible for overseeing the company’s data protection strategy and its implementation to ensure compliance with GDPR requirements.
Data Governance Officer provided the Data Governance framework – Axon, Data Privacy Management, and Test Data Management to be leveraged. He has collaborated with the Legal team to address the GDPR regulatory policies and has started defining the corresponding processes, systems, glossaries, datasets, and attributes in Axon required to meet the compliance requirements.
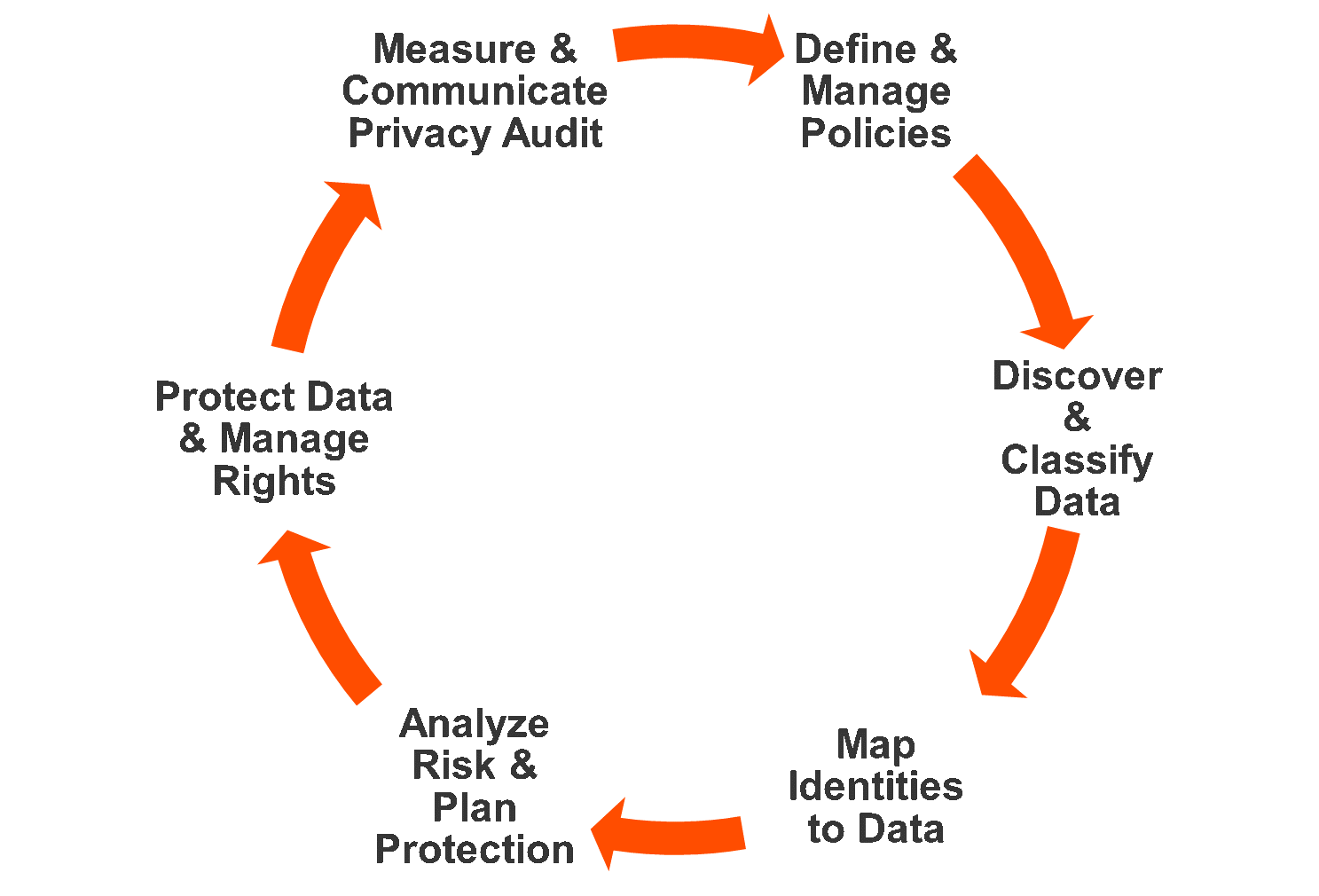
Figure 5. Data Governance Framework for Privacy Regulations
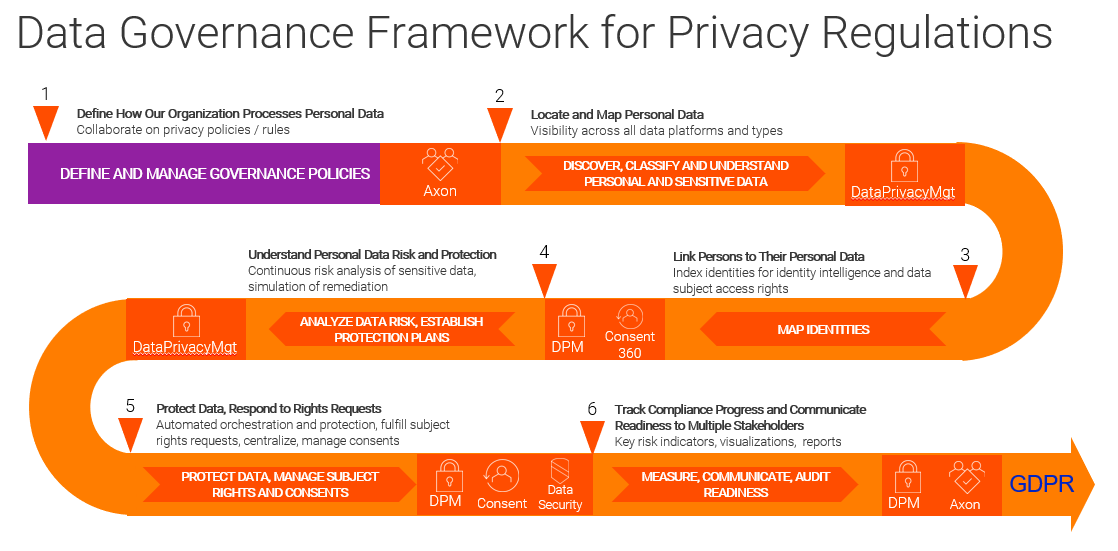
How to handle government policies:
- Connect people, processes, and systems
- Manage privacy policy response
- Monitor and report on compliance
Let’s start the case study with two prominent users: a Data privacy officer (DPO) who is Otto Owner and a process owner Mike Manager. Otto wants to ensure that the process is not legally exposed and wants to make sure that they have evidence to show that they have implemented the policies and processes to ensure that they meet the obligations imposed by GDPR principles. Otto (The DPO) logins to Axon and make sure that having all the privileges to access the rest of the data.
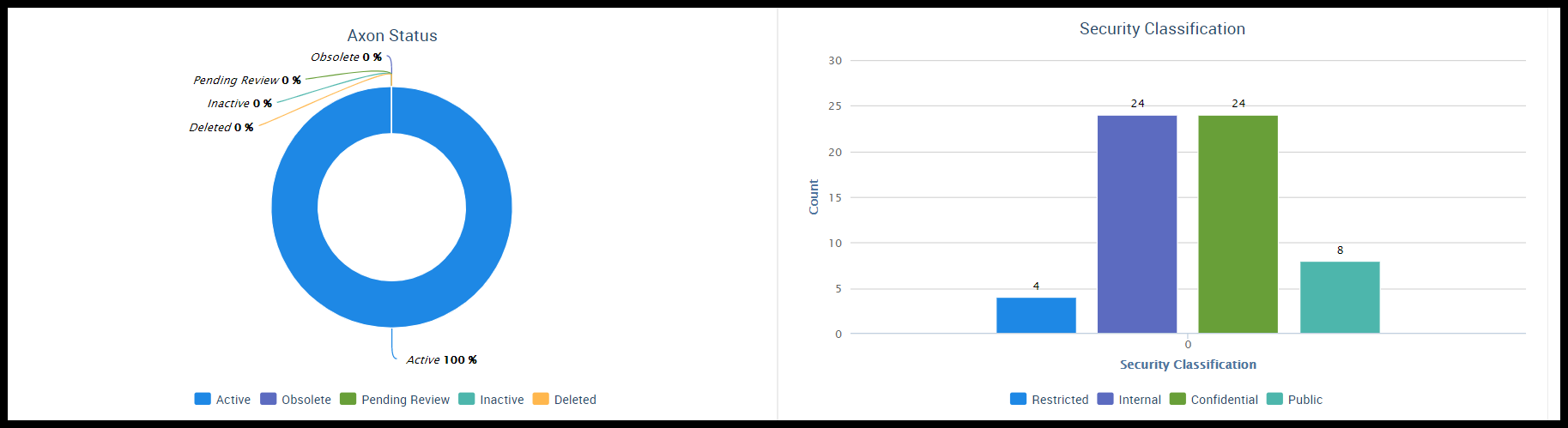
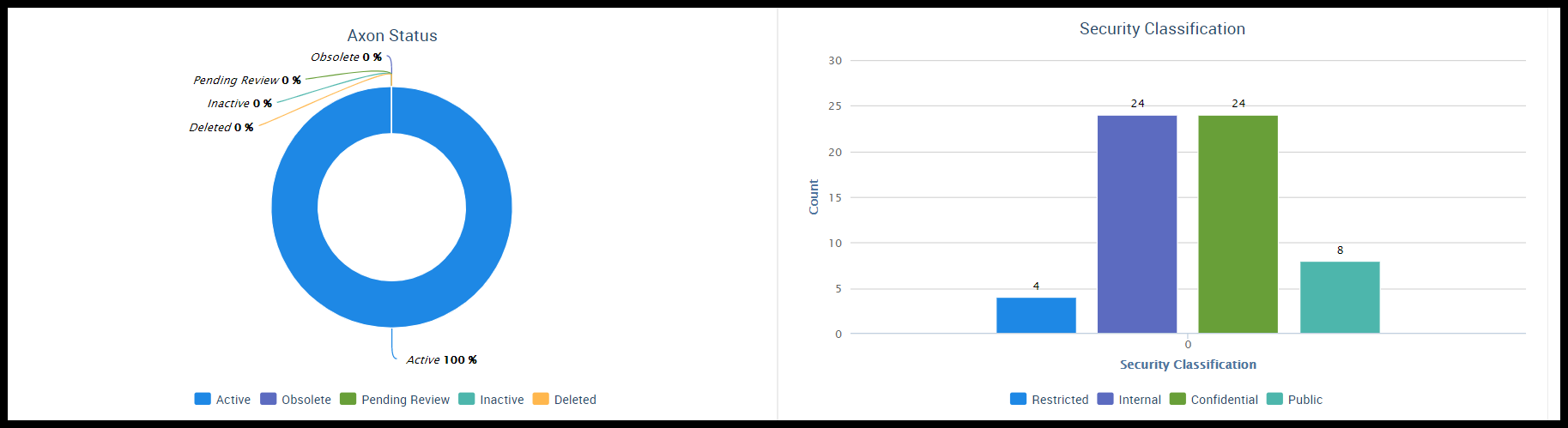
Otto (The DPO) now searches for GDPR policy with the help of the Unison search and looks for the linked Glossary and how it is linked to sensitive data like the First Name, Last Name, Gender, Date of Birth, etc. and he can see the dashboard. The dashboard tells him how much has been approved, Axon Status and Security Classification.
Figure 6. Glossaries linked to sensitive data
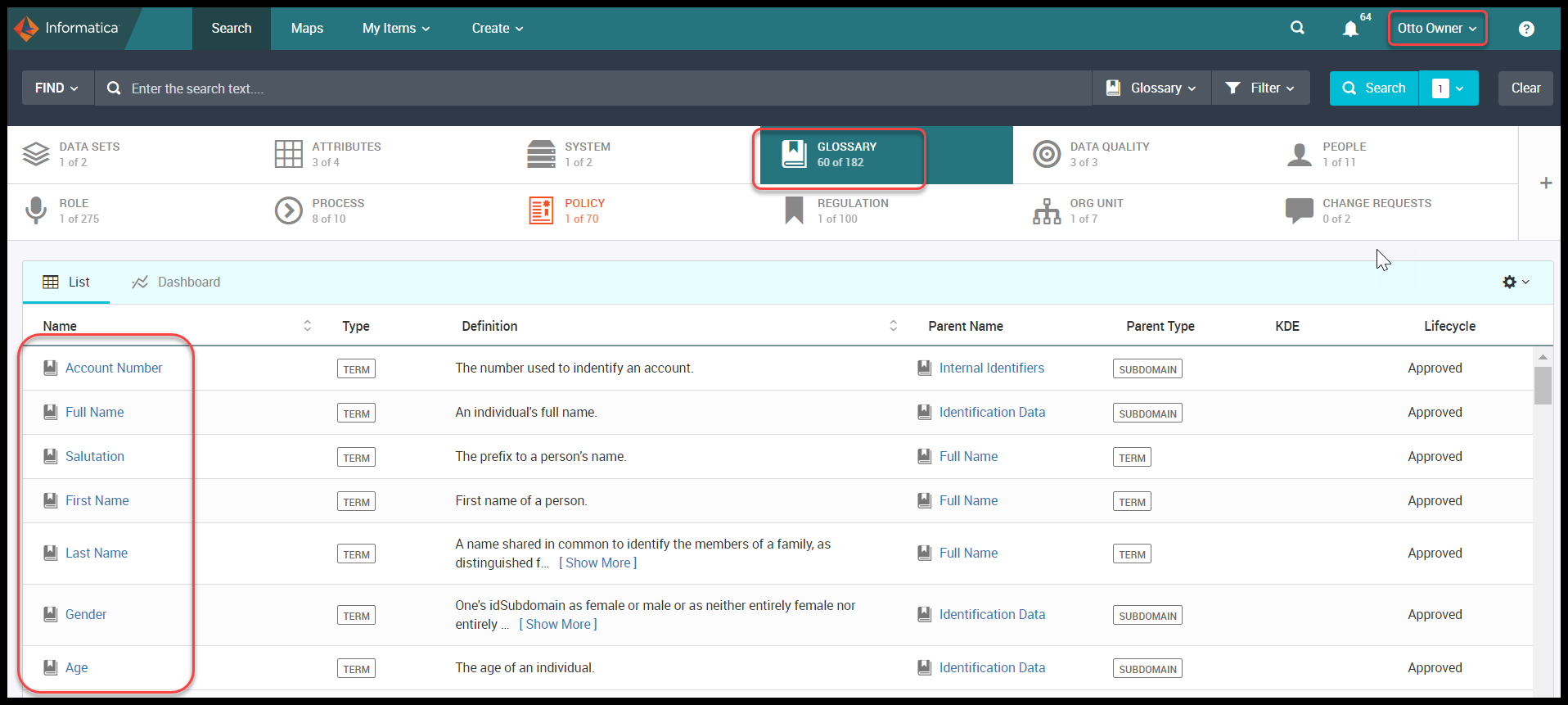
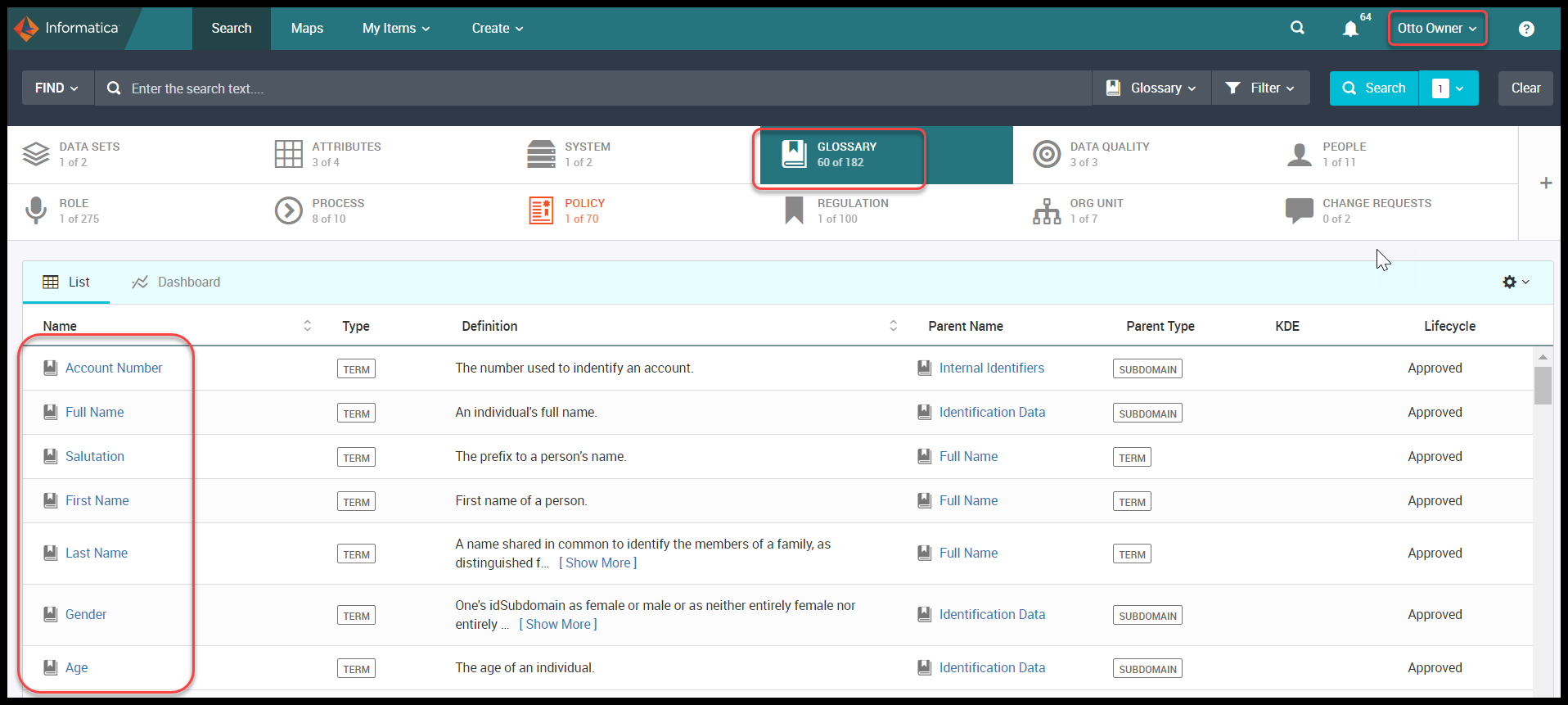
Figure 7. Glossary Dashboard
GDPR is external and has been defined with 99 Articles, DPO (Otto) now wants to understand how this regulation has impacted the policy and must figure out how it impacts the day to day running of the business. Hence the GDPR policy is linked to the GDPR Regulation to walk through.
Figure 8. GDPR Regulation
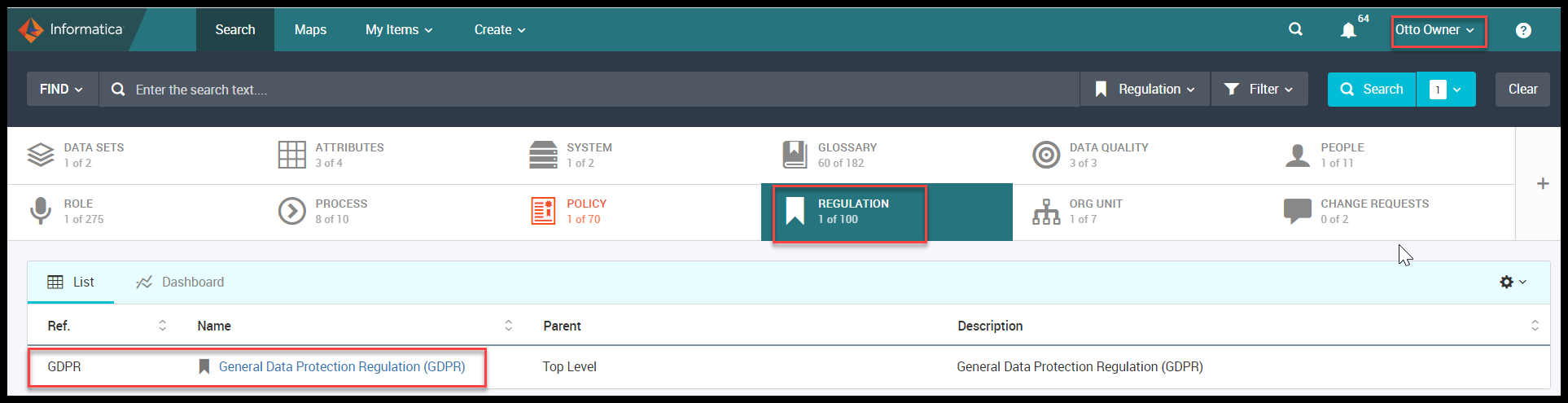
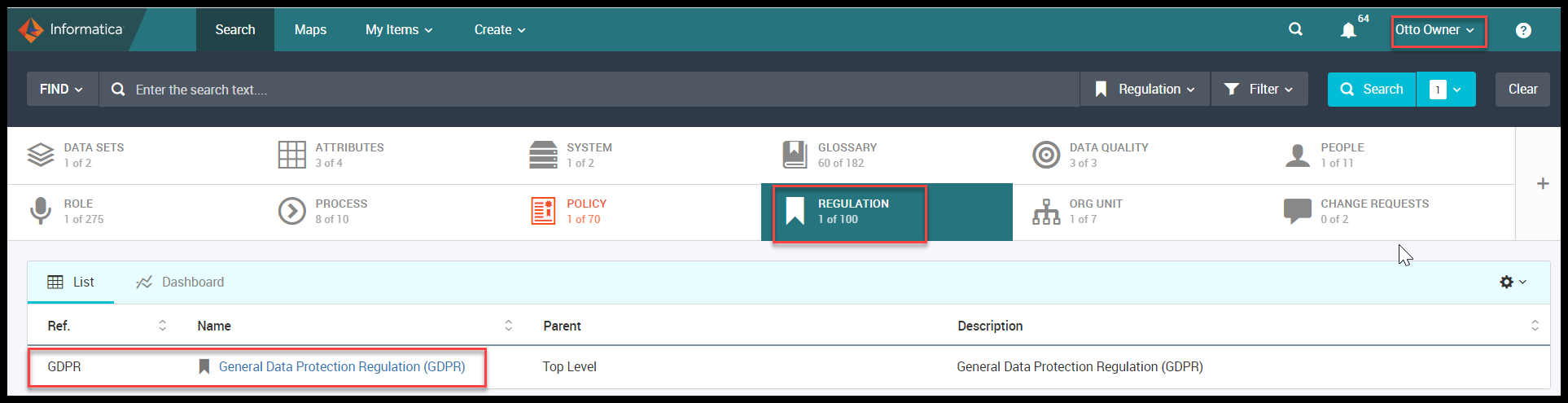
Figure 9. Components of GDPR Regulation
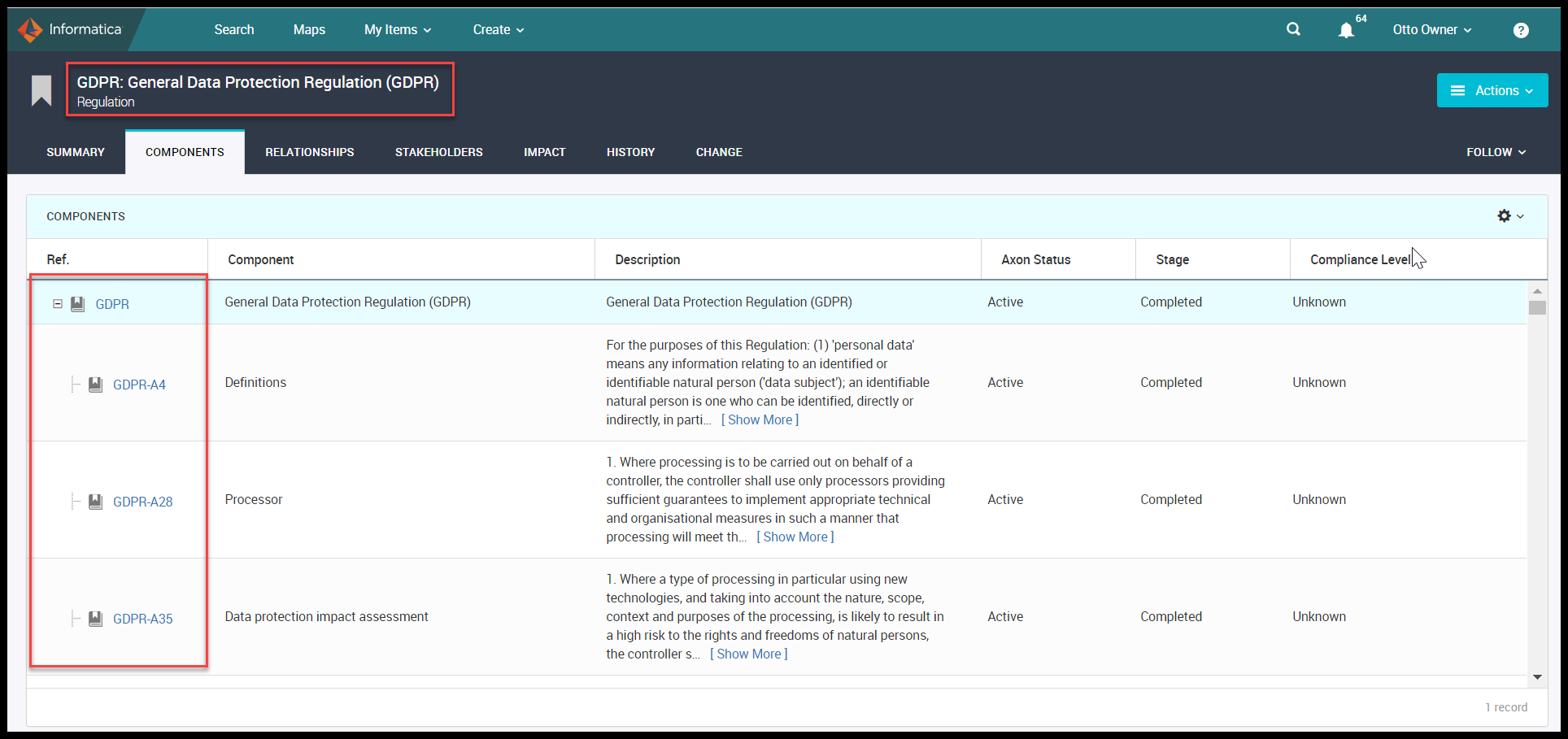
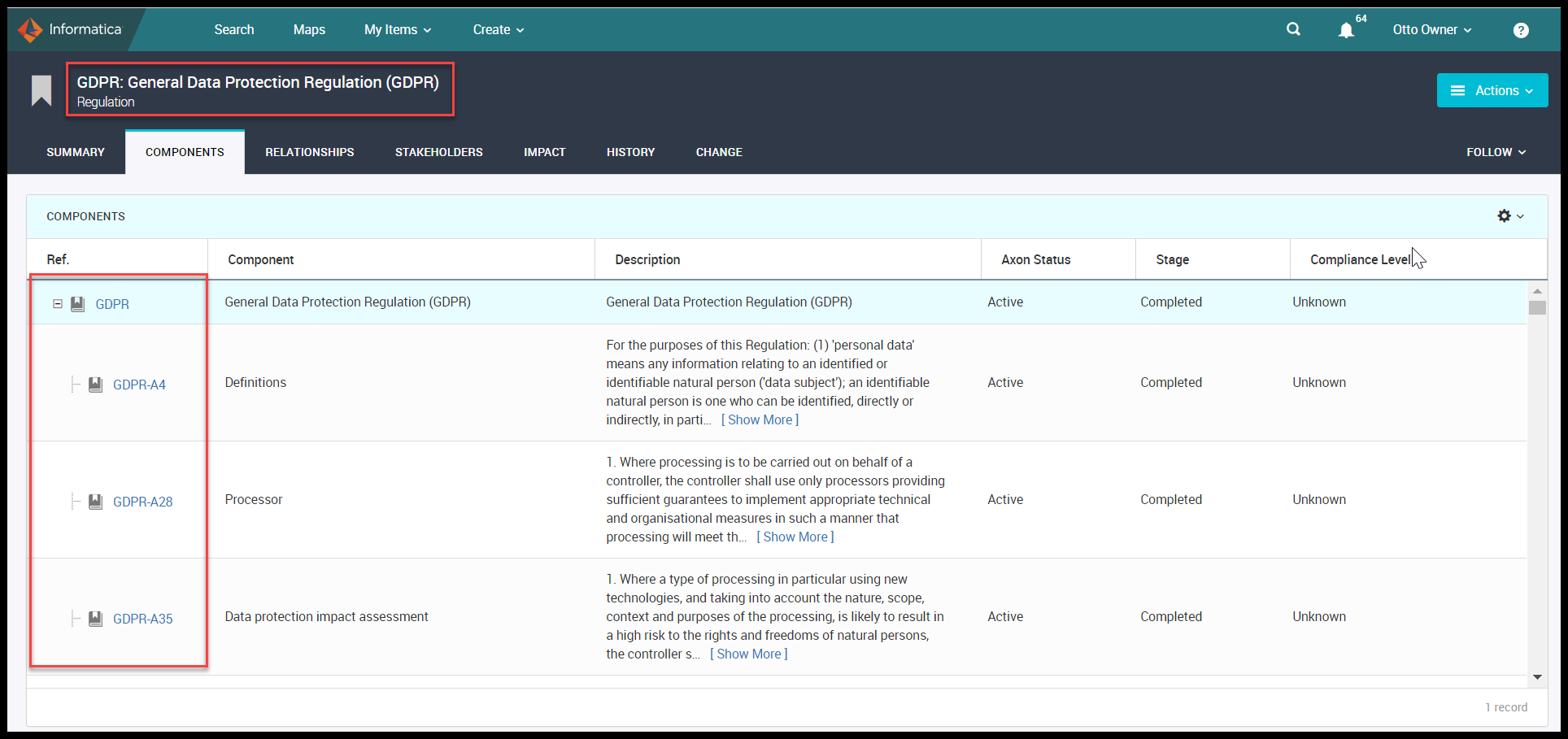
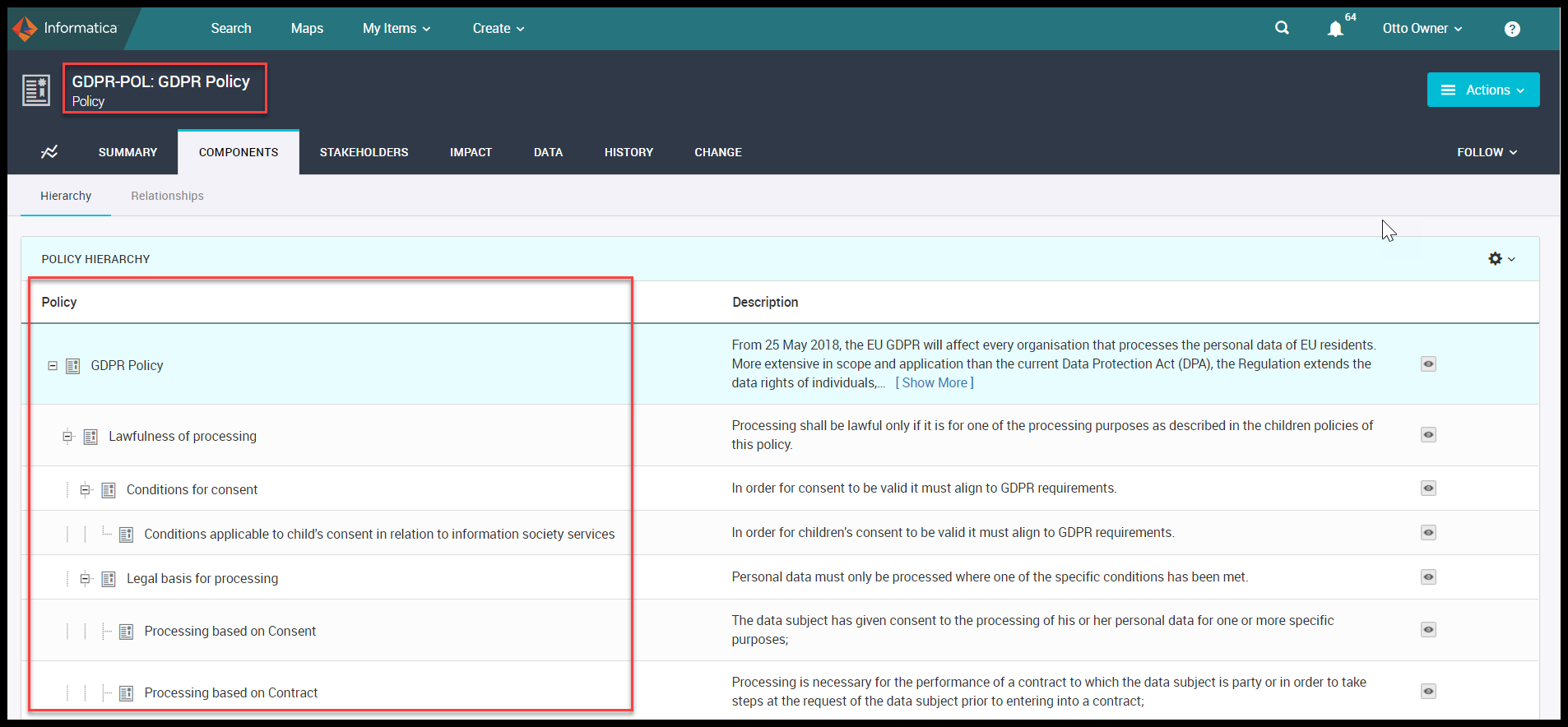
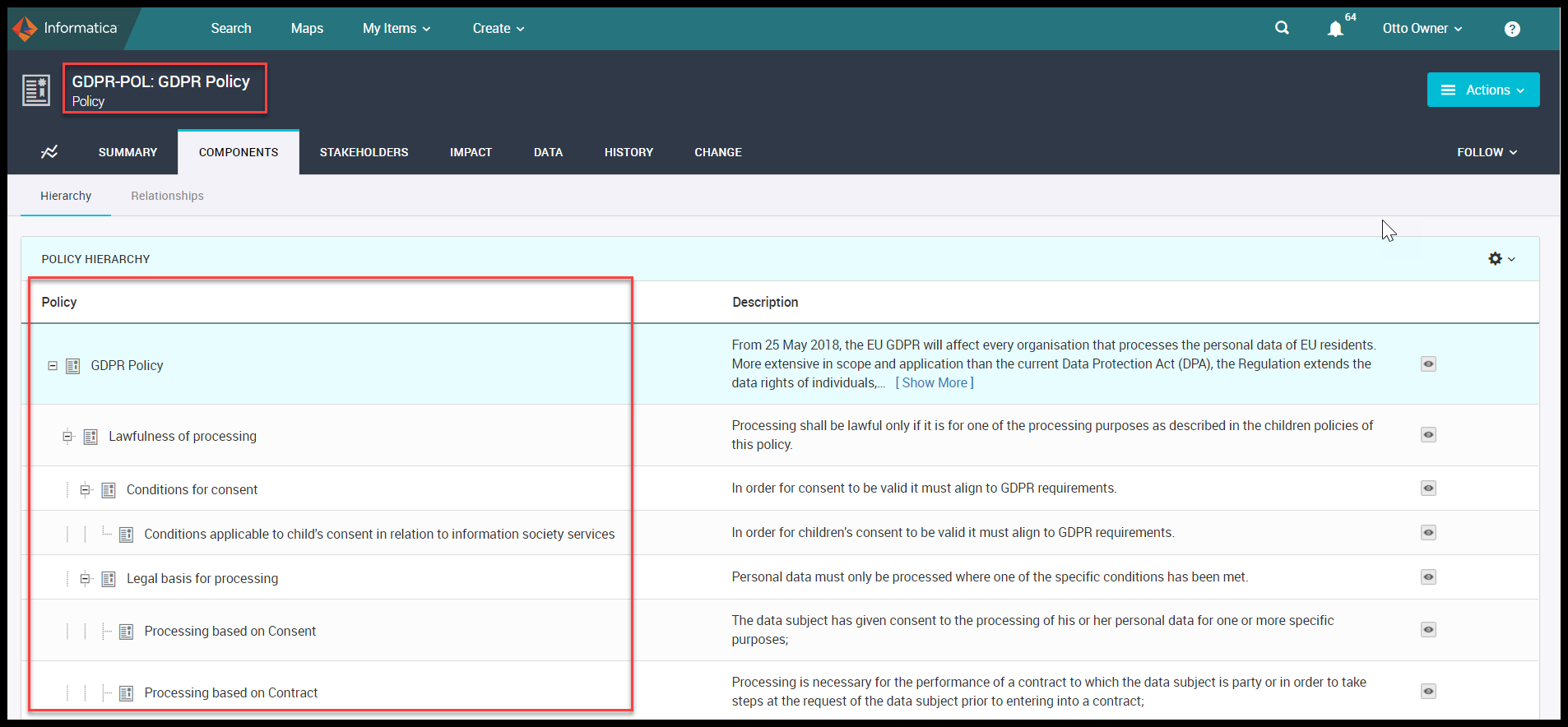
GDPR policy is the Axon asset and it has a better description. It has a link below that takes you to the table of contents on the Articles. Components of this GDPR policy describes all the policies.
Now DPO decides that the best way to implement the GDPR program is to categorize the purpose of processing and as it is defined in the GDPR.
The process that is using personal data like PII – Personally Identifiable Information, must be linked to know the purpose of processing. This is the policy requirement and must be linked to the process using that personal data. Also,there needs to be a lawful basis for processingpersonal data that could be based on the consent or the contract you have.
Figure 10. Sub policies of GDPR Policy
Now DPO(Otto) wants to see that the process “Data Privacy Impact Assessment (DPIA)” is conducted. DPIA shows how Personal/Sensitive data is processed across the process. DPO (Otto) asks the process owner to act on the Client Onboarding process to check whether the client data is treated appropriately under GDPR.
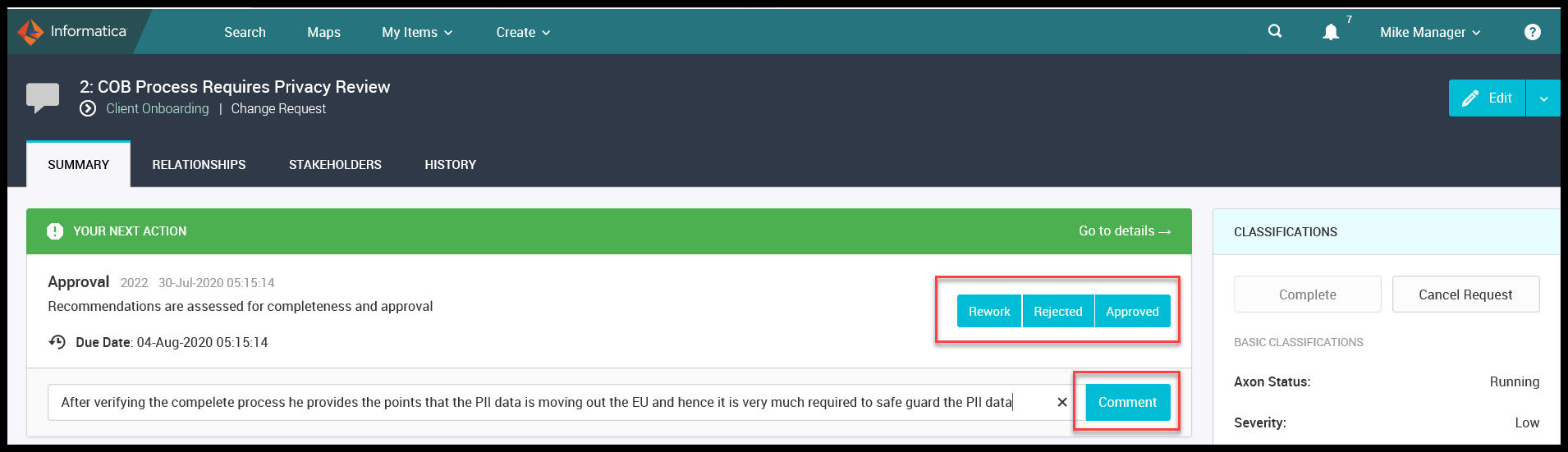
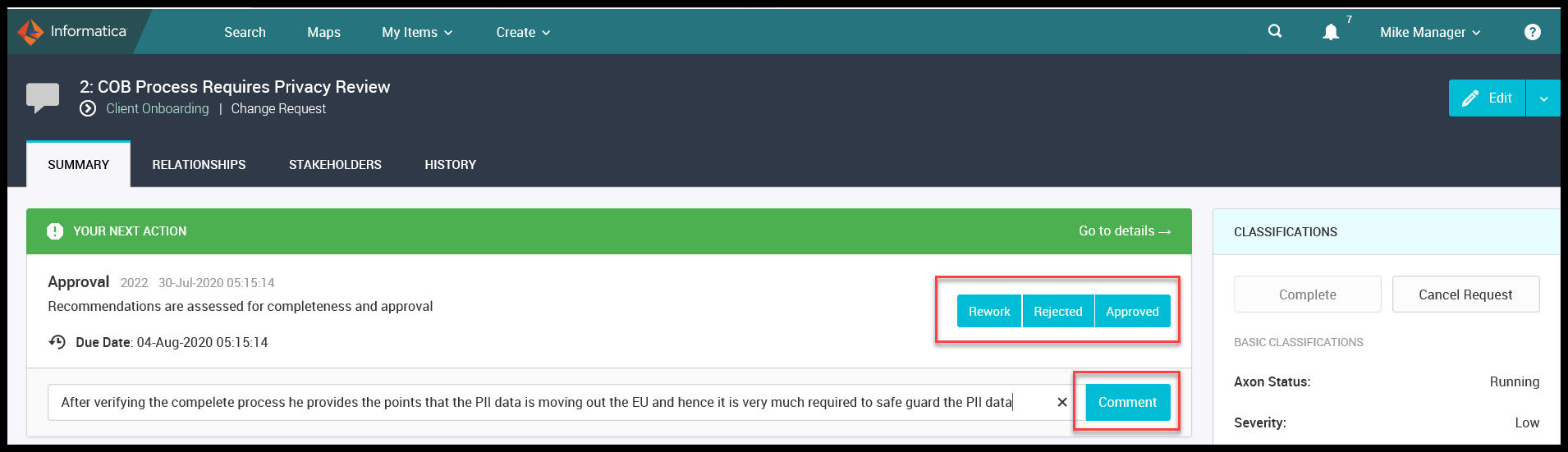
Sally Steward being the process Steward logs in a change request saying COB Process Requires Privacy Review.
Figure 11. Change Request
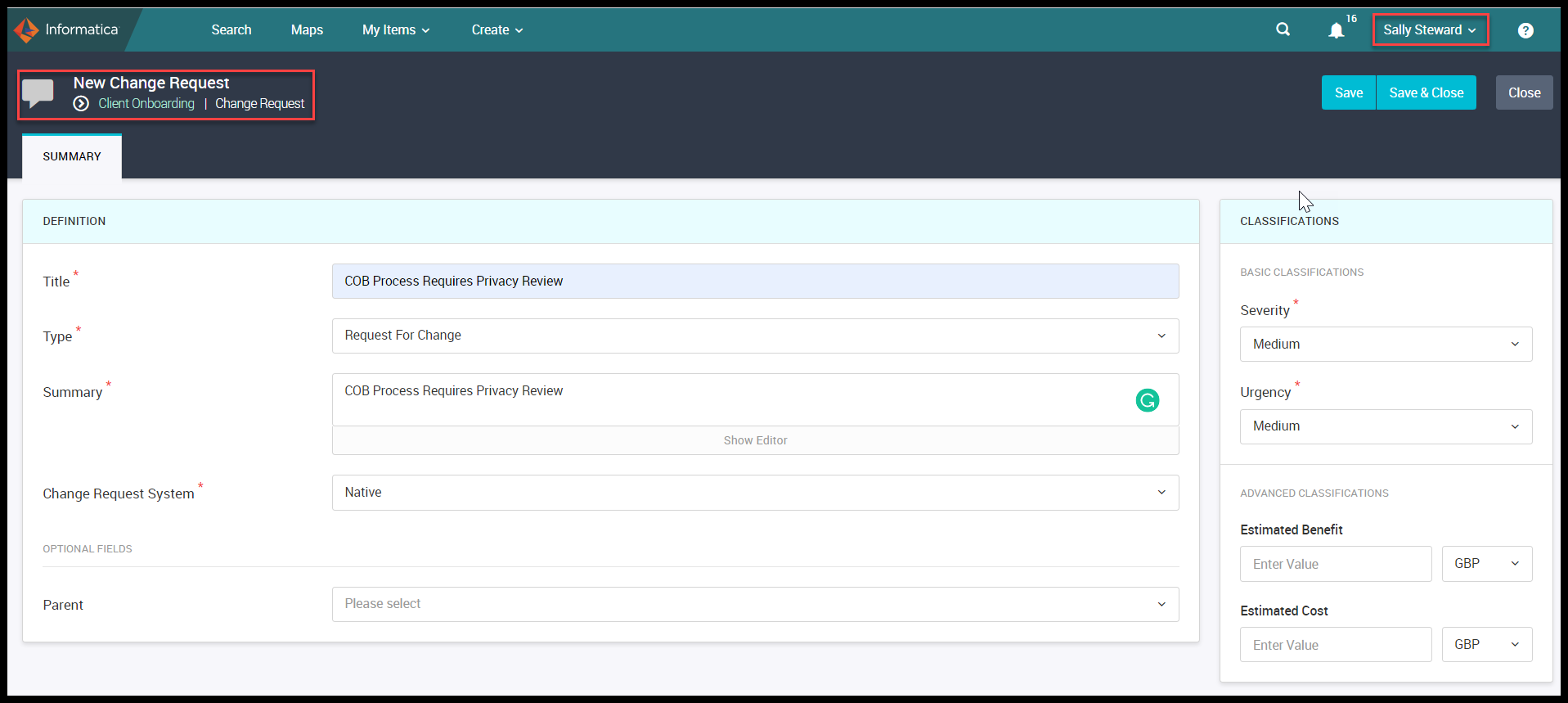
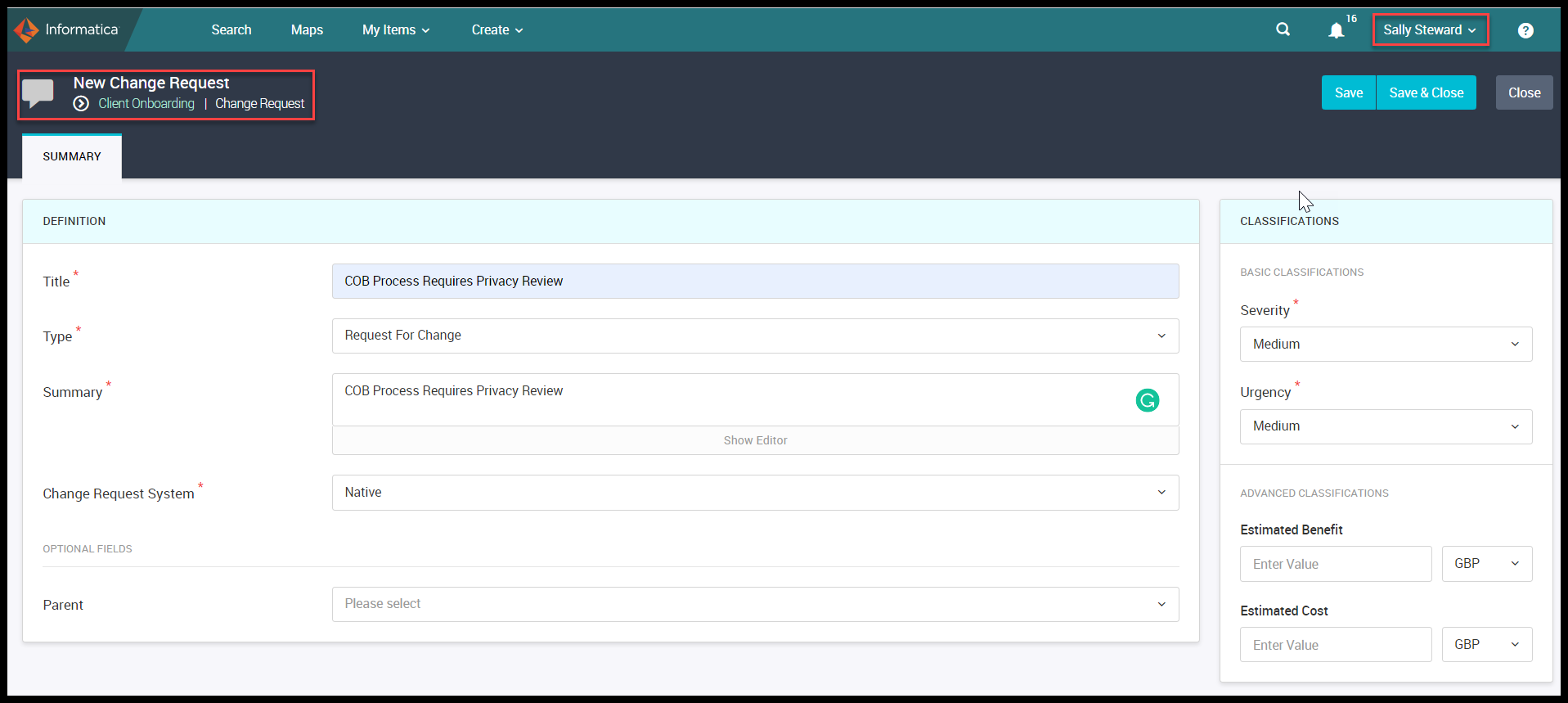
Once the change request is saved then Sally selects the workflow and if required uploads any related document and Says ‘START’.
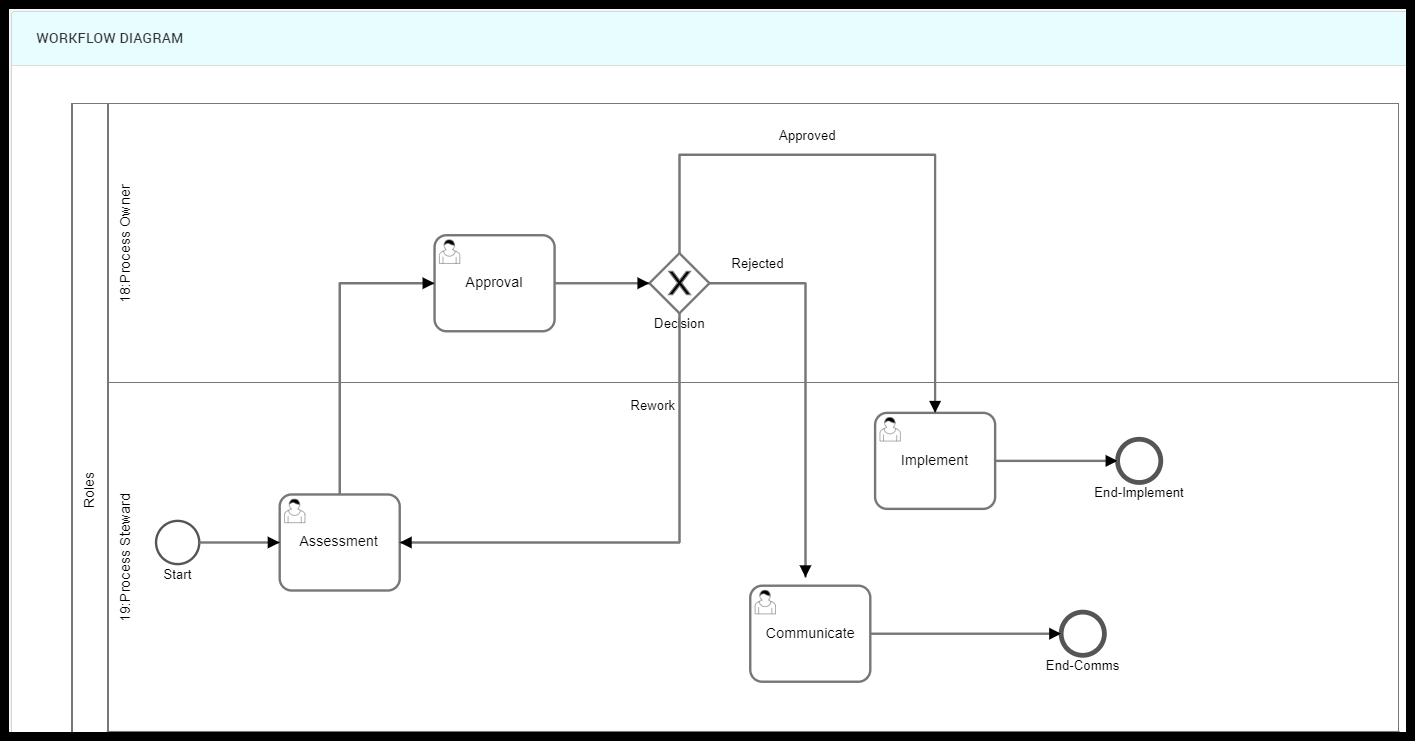
Here is the workflow diagram.
Figure 12. Workflow Selection
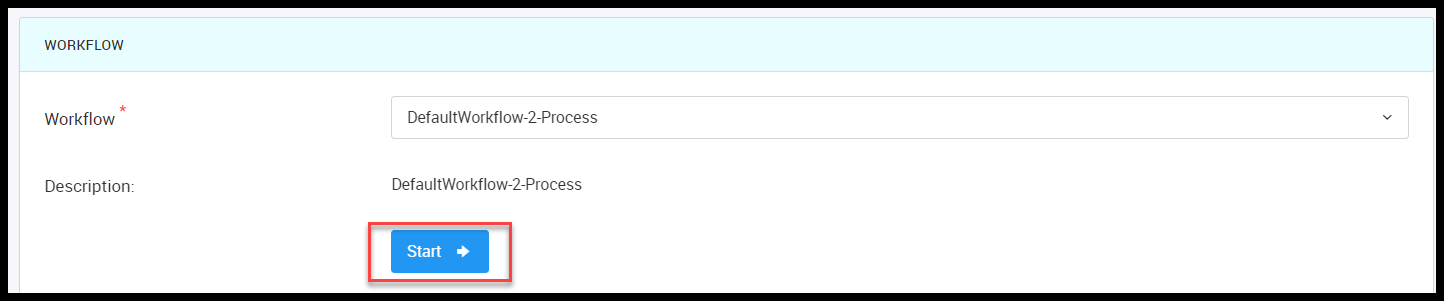
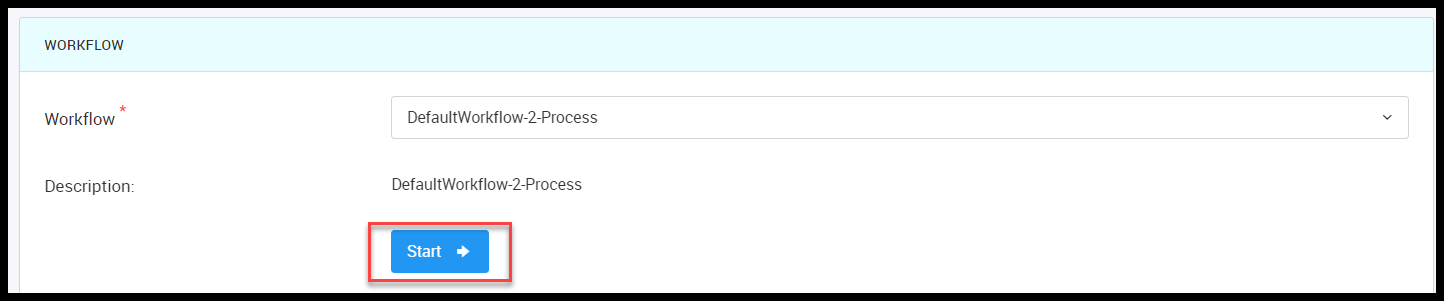
Figure 13. Workflow Diagram
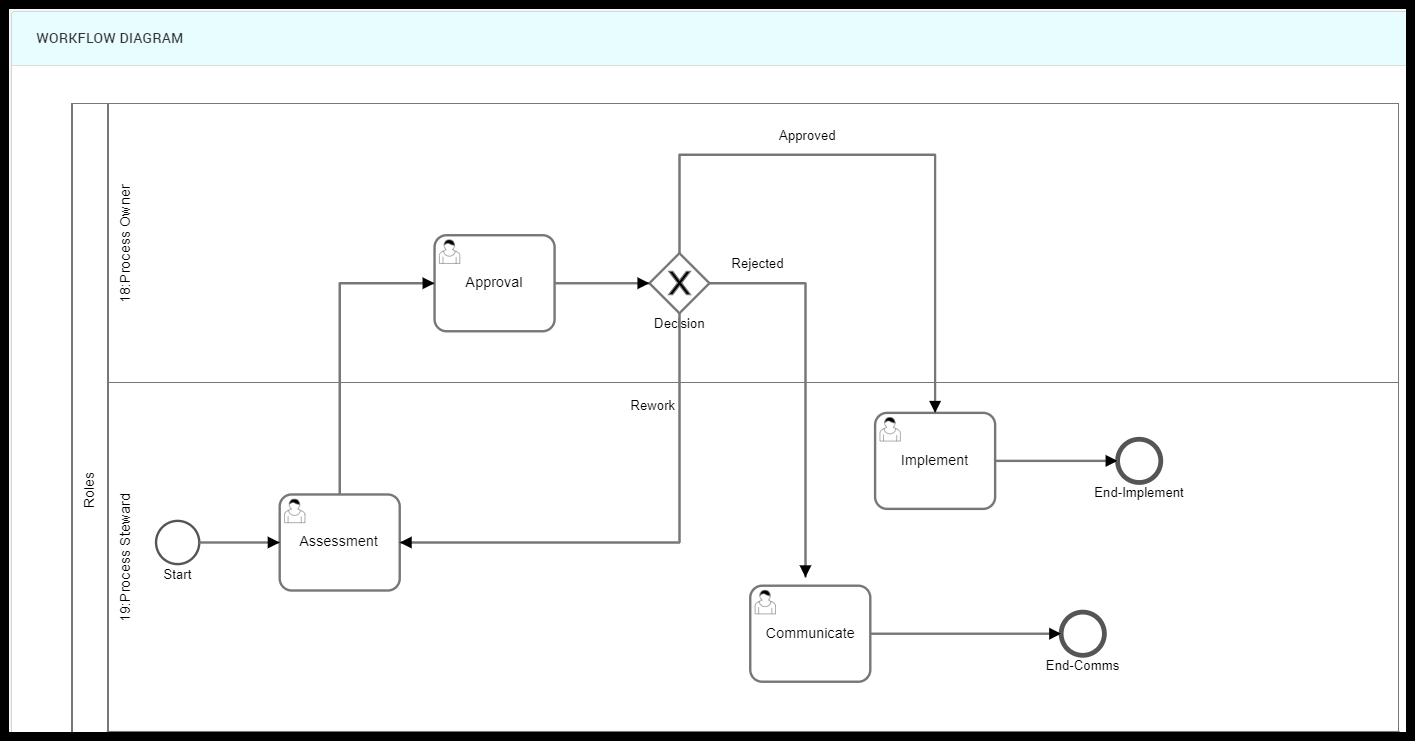
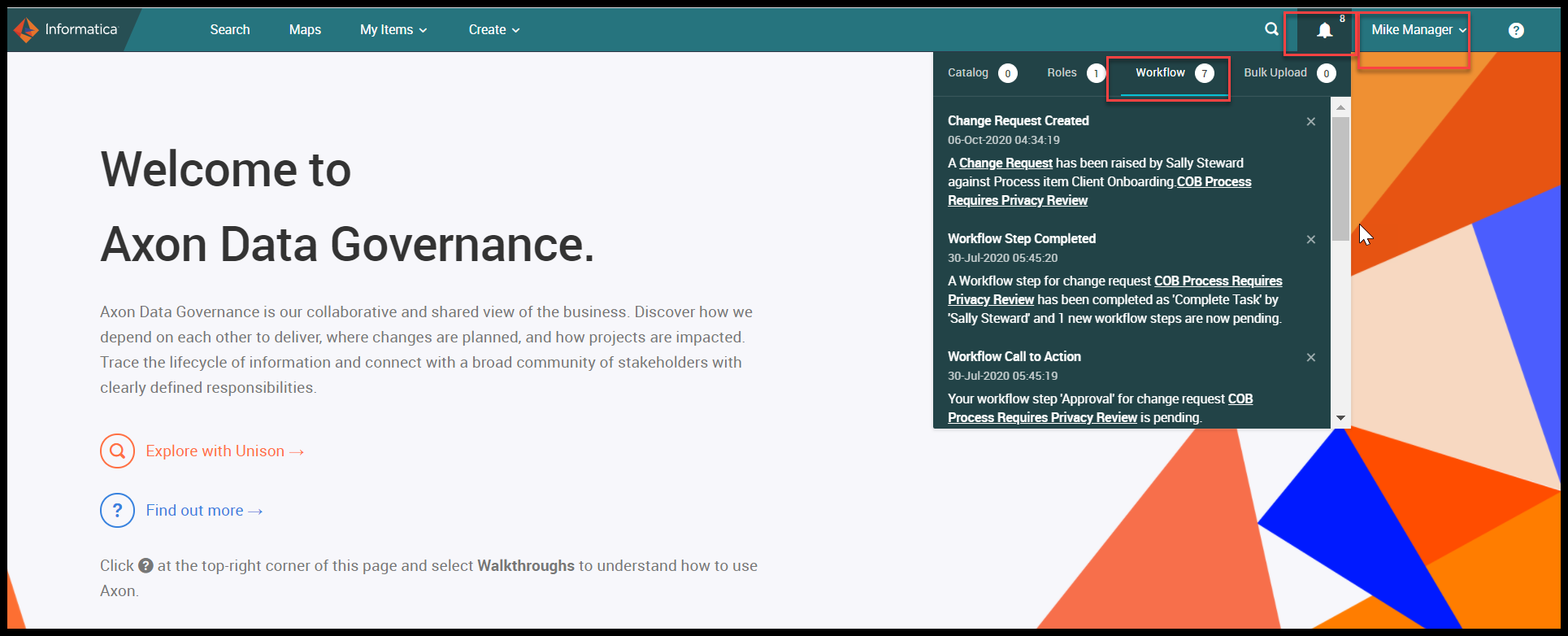
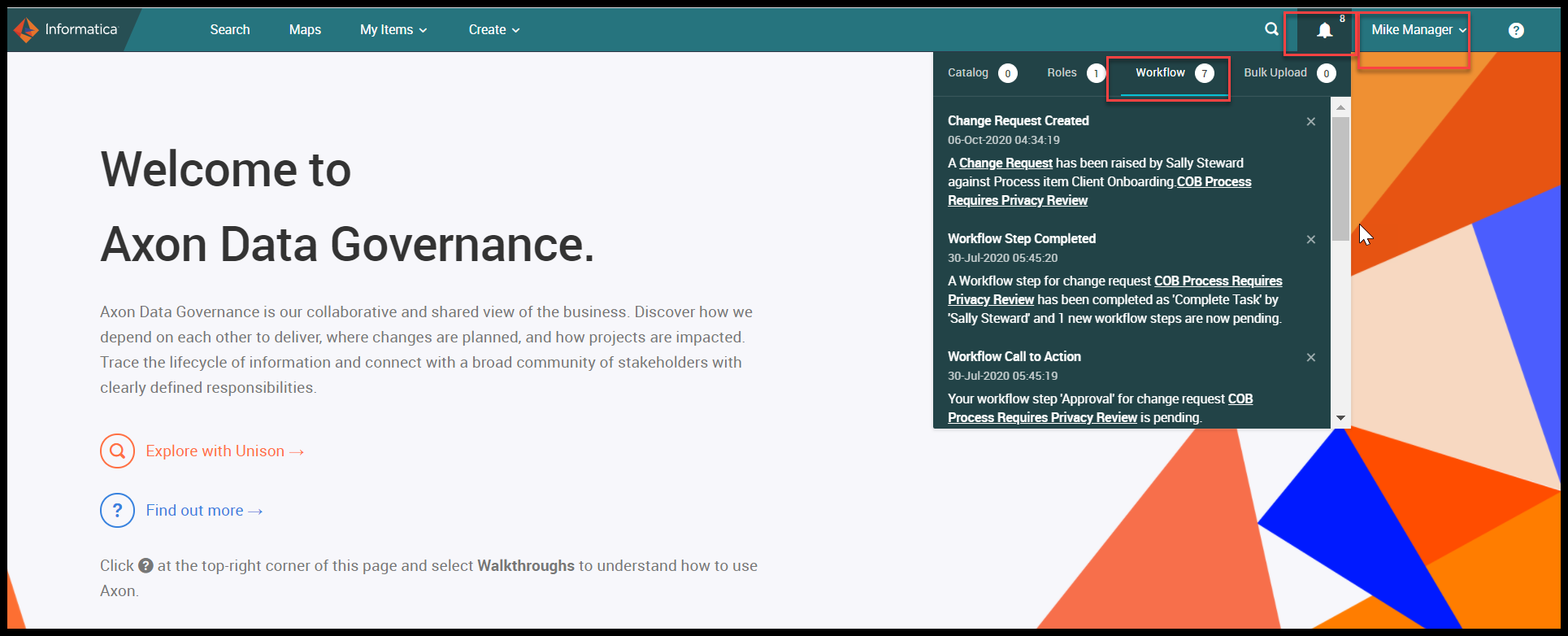
Now the workflow step is moved to the Process Owner – Mike Manager and he logs in to Axon and sees the workflow notification under workflow and clicks on the COB Process Required Privacy Review task.
Figure 14. Workflow Notification
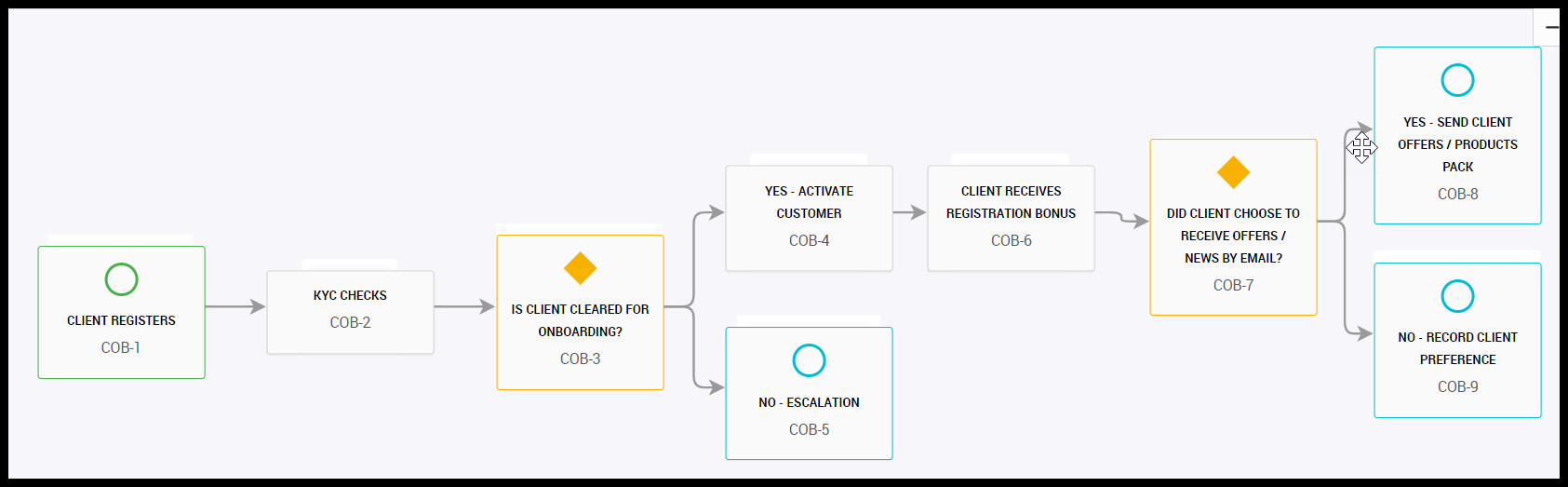
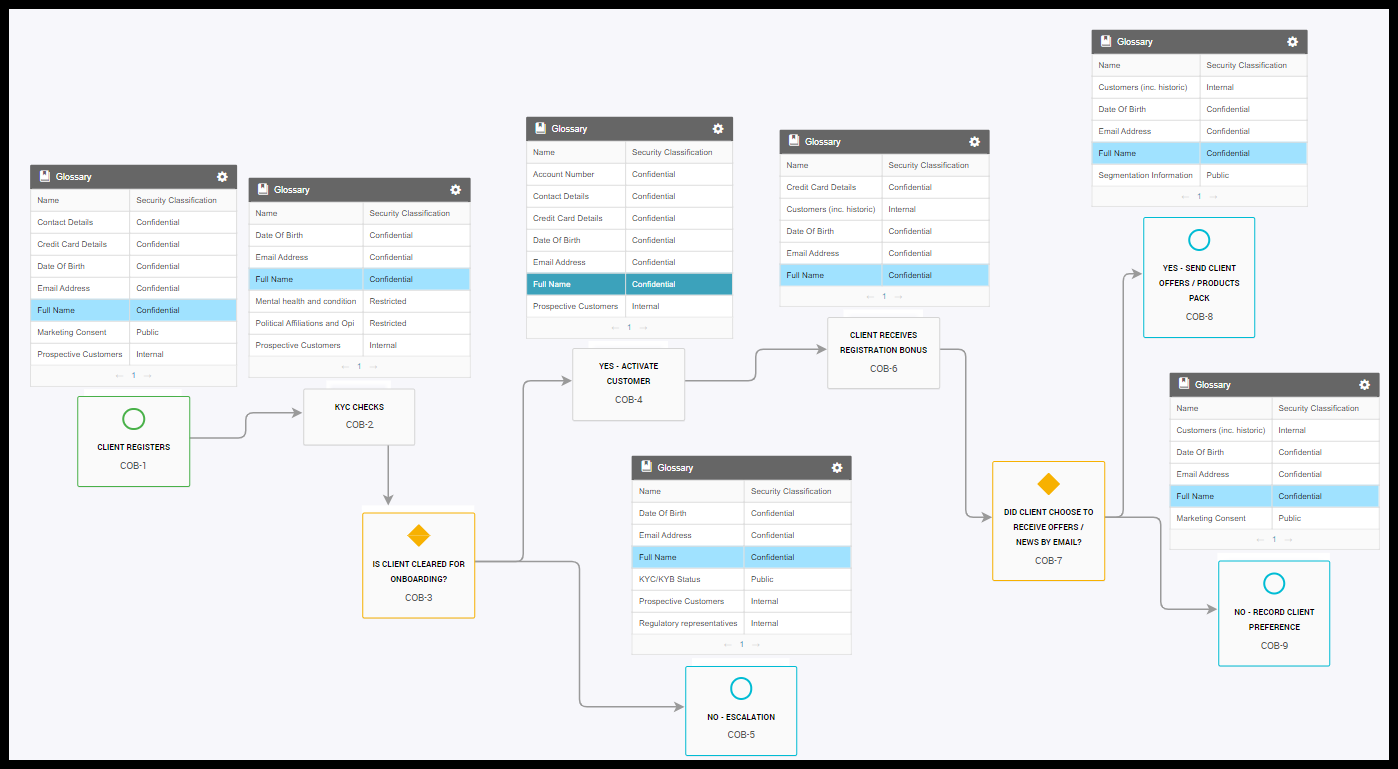
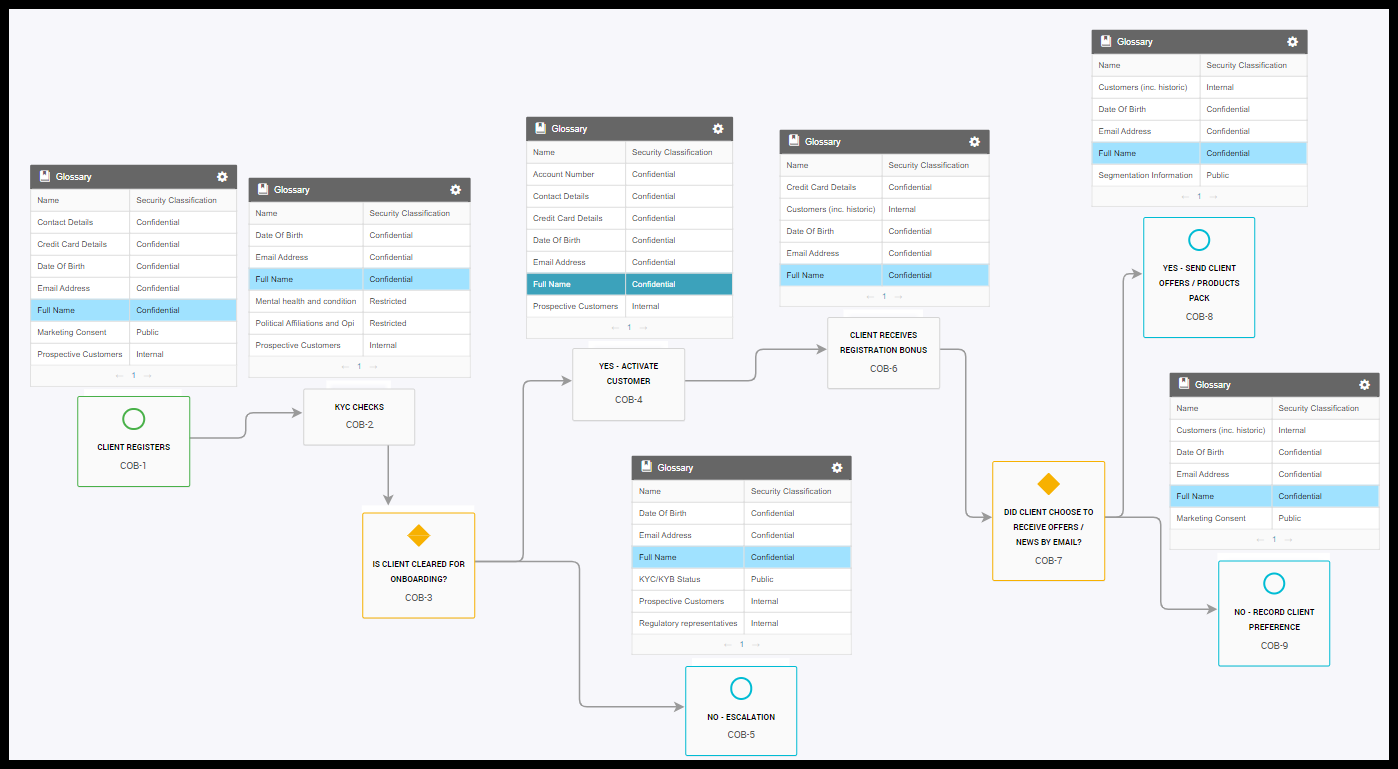
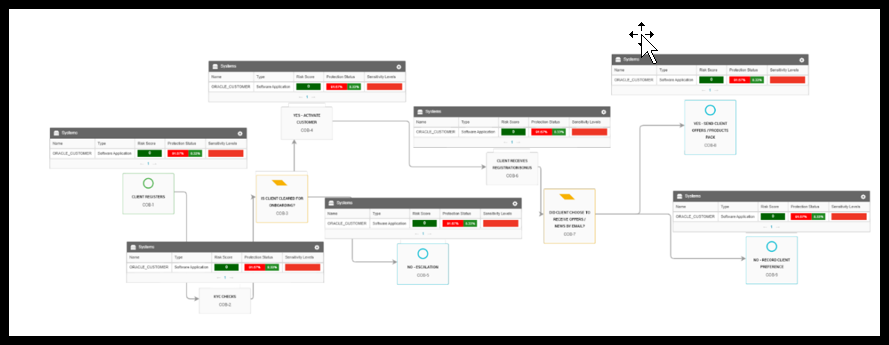
By seeing the details in the workflow Mike opens the Client Onboarding process (COB) by using the Unison search and clicks on the ‘Components’. This shows the complete flow of the COB process and all the sub-processes. The subprocess is linked with the help of the import template.
The process starts from ‘Client Registration’ followed by a KYC check and after condition, if KYC is good, it moves to Activate the Customer and the client receives registration process and after condition, match Client receives offers in the ‘Yes send client Offers/Products Pack’, If not then there’s No record client preference. This is the overview of the Onboarding process.
Figure 15. COB Process Diagram
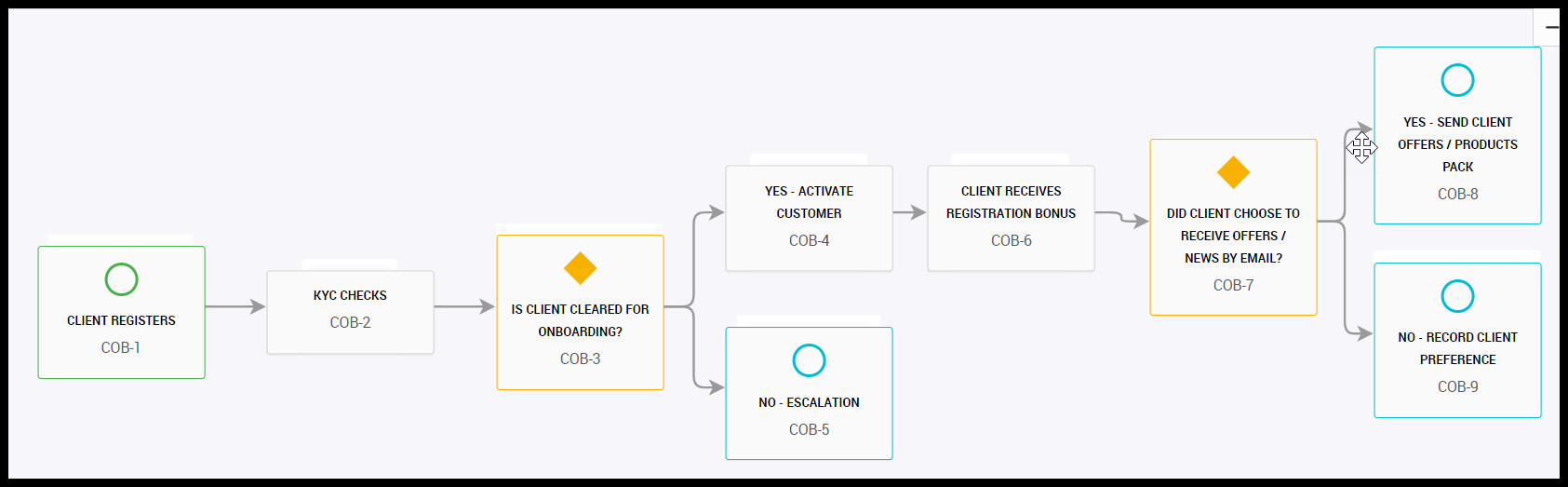
To see the personal data moving through the process, Mike opens the Glossary overlay. The below Glossary overlay highlighted with the Full Name and personal data shows the movement through the process. He adds the security classification in the same overlay, and that shows that the data is confidential, protected, or restricted. He sees that there are personal data that are restricted and it’s a special category data and it must be treated even more carefully, and by now he understands what kind of personal data he is dealing with and how it is moving through the process.
Figure 16. Glossary Overlay in COB Process
How to manage personal and sensitive data:
- Continuous discovery of data stores
- Intelligent data classification
- Identify dangerous data flows
- Understand user-access
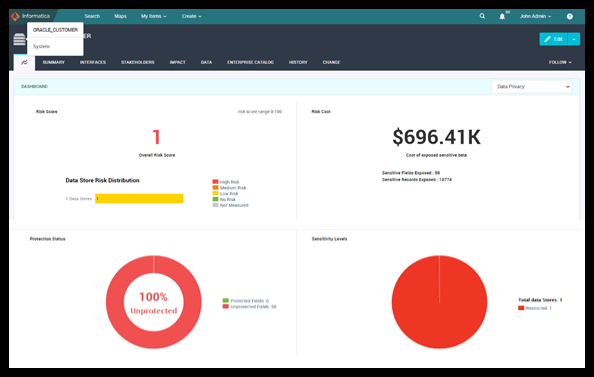
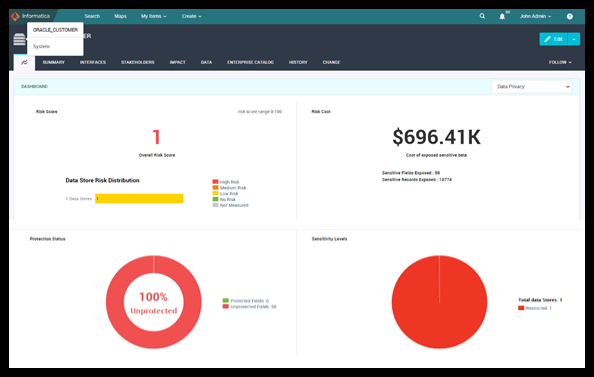
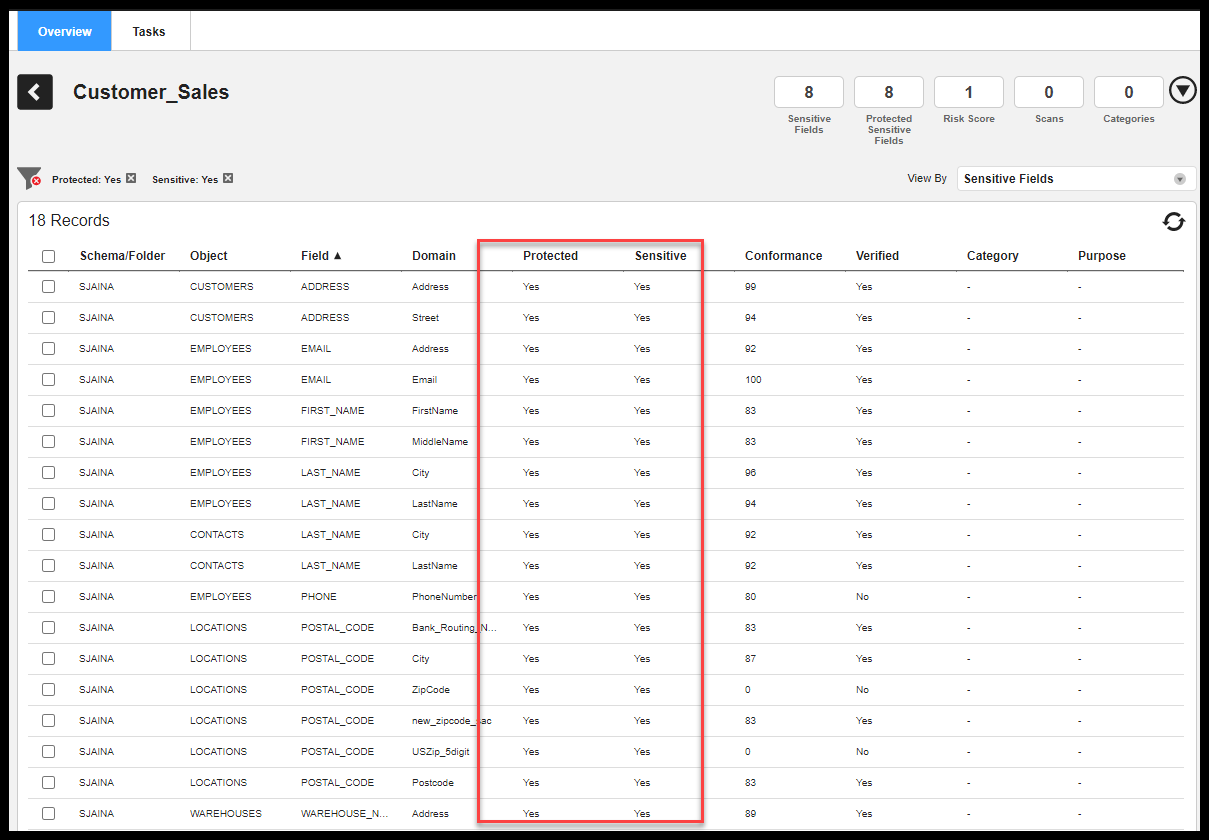
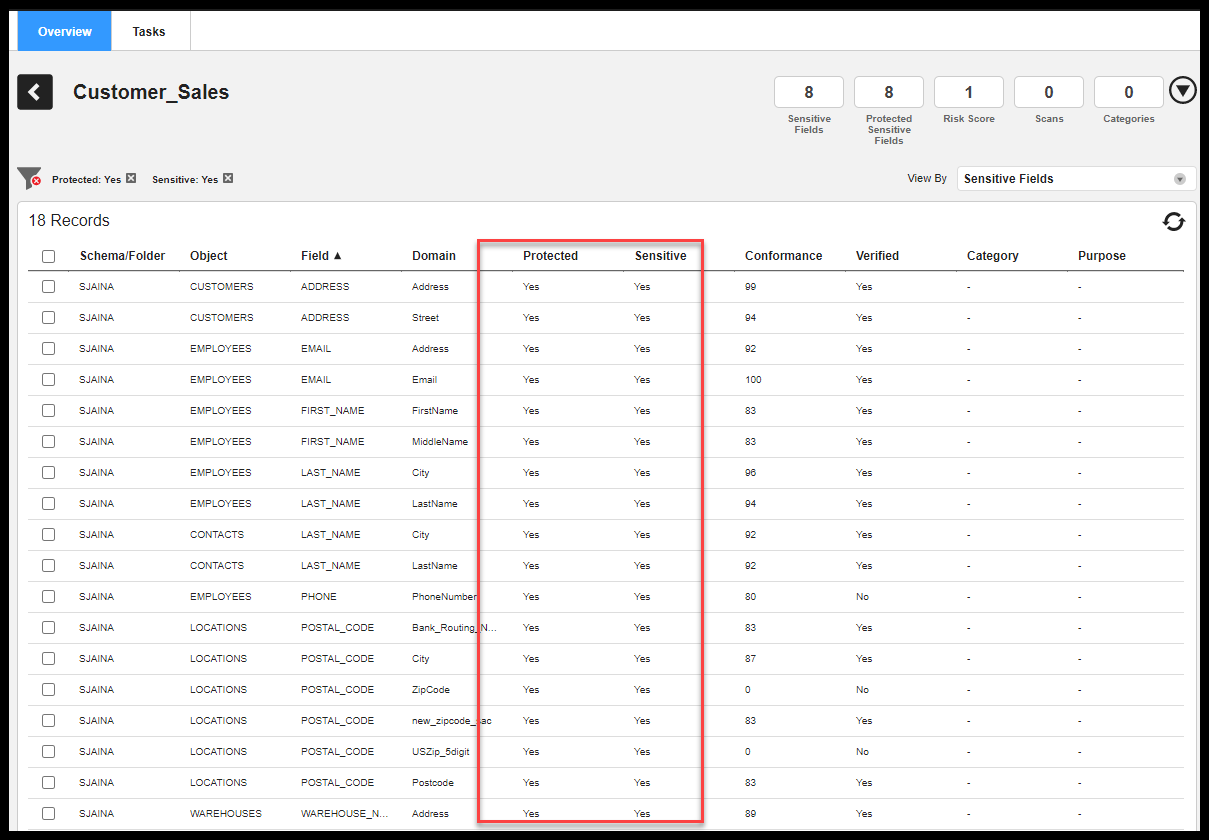
Data Privacy Management helps to discover and classify the data and provides information on whether sensitive data is protected or not. Mike now logs in to the Data Privacy Management tool and scans the Datastore (resource/system) and selects the GDPR classification which is available in the tool. He understands the protection status, sensitivity level, risk score.
Figure 17. Dashboard of DPM
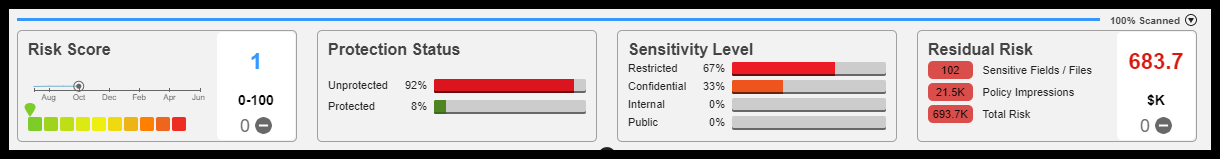
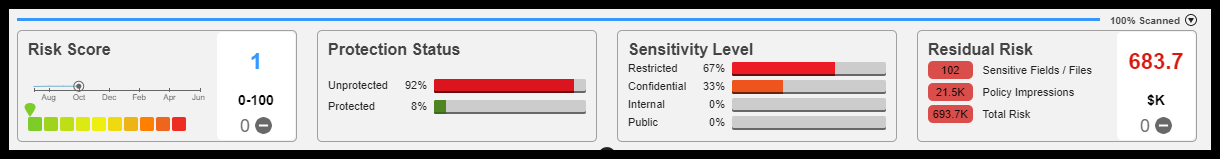
Figure 18. Sensitive Data by Data Store Group - GDPR
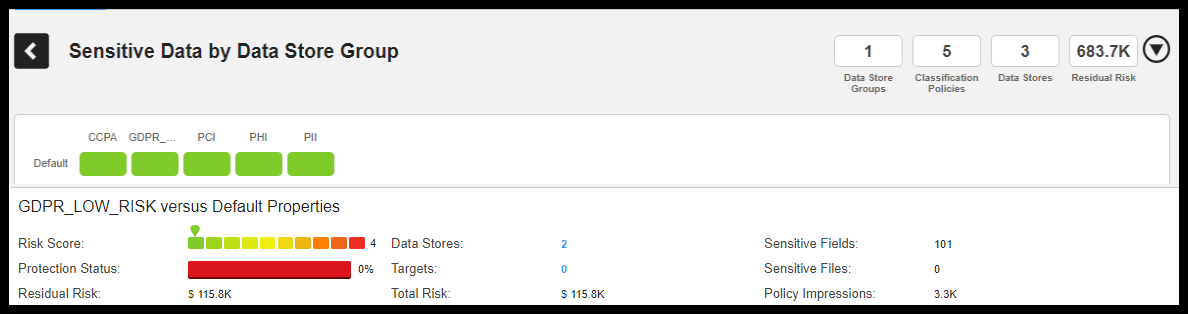
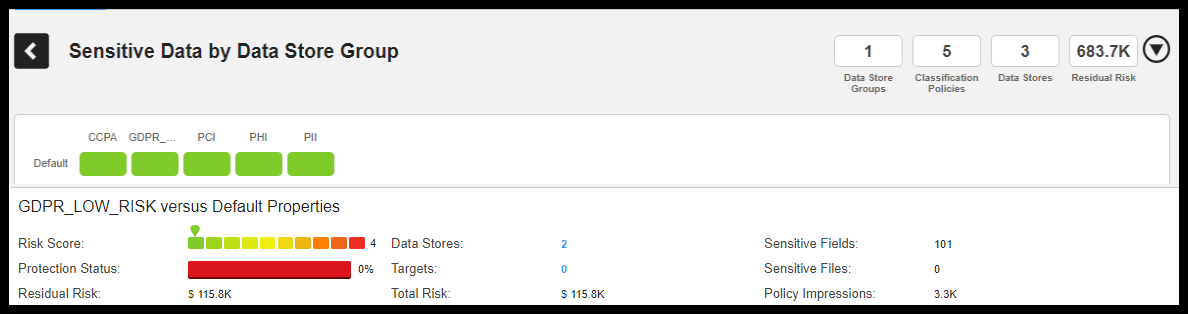
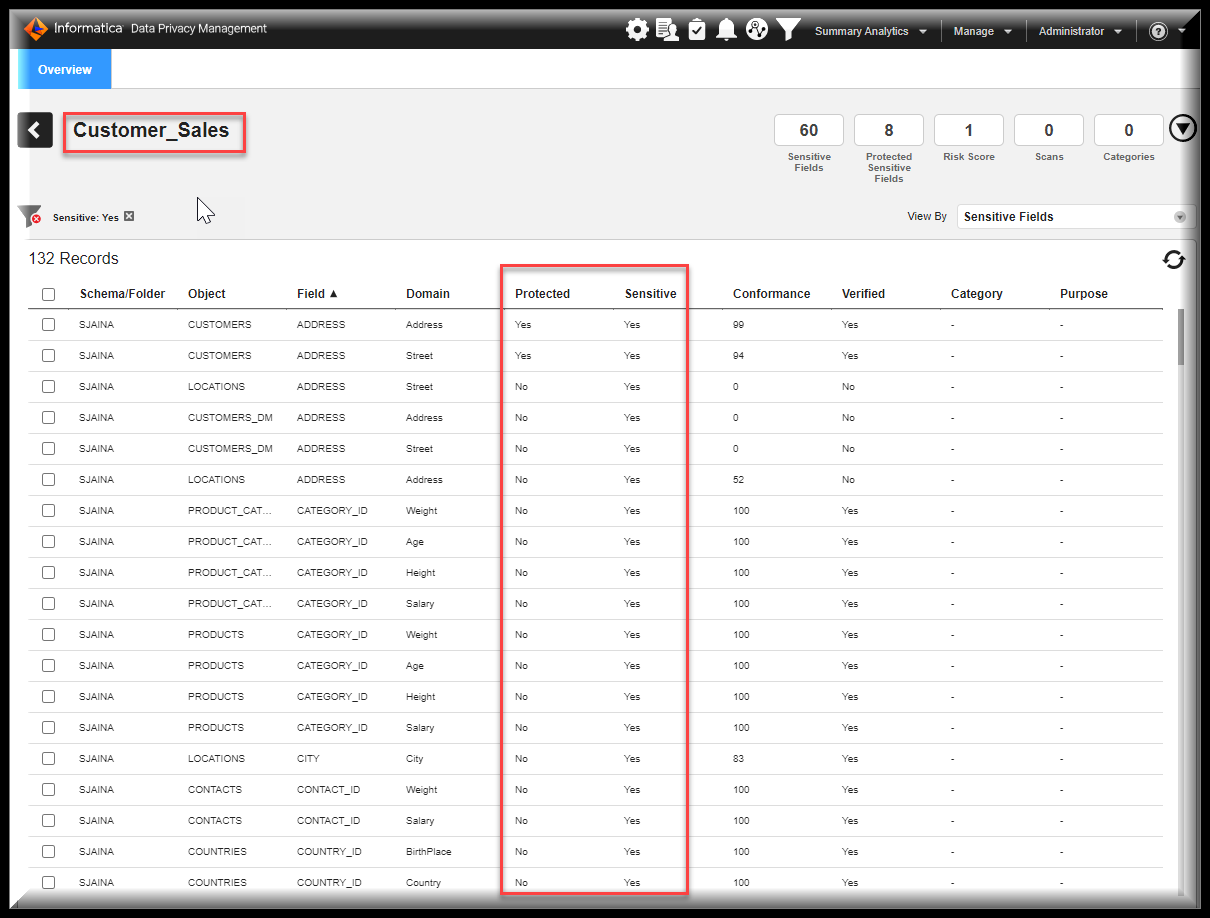
Figure 19. Protected and Sensitive Data
The DPO (Otto) can find the Privacy dashboard in Axon. The result from DPM is extracted and shown here.
Note: DPM and Axon integration should take place and the user must link the Classification policy to the GDPR policy.
Figure 20. Privacy Dashboard in Axon


How to Map Identities?
- Link identities to sensitive data
- Intelligence on location, systems
- Intelligence on use, access
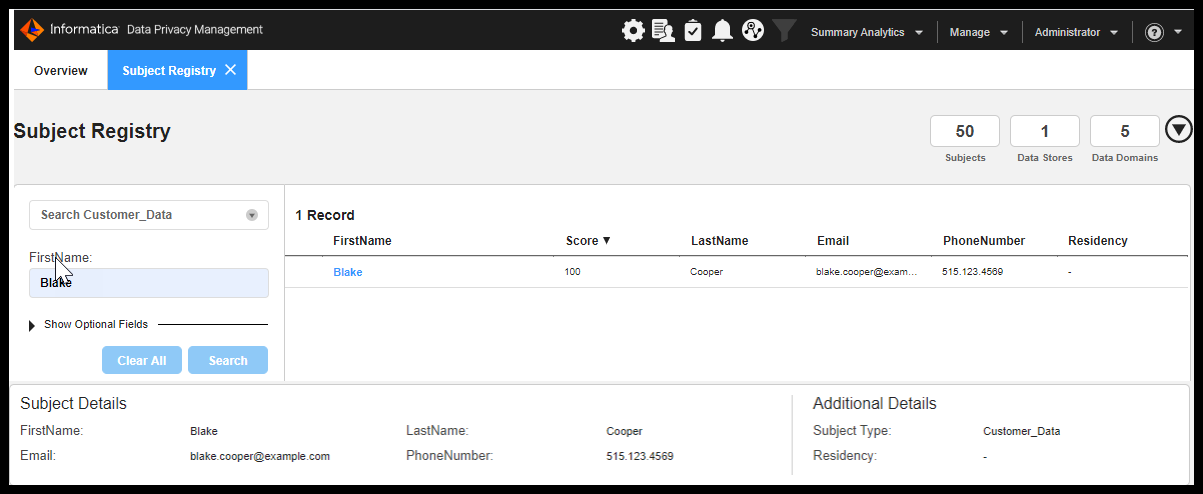
SUBJECT REGISTRY in Data Privacy Management provides identity mapping capabilities that support data privacy legislation such as GDPR Specifically. Subject Registry maps individuals with the data that you maintain on them and provides a detailed report on the location and type of data.
Mike can now quickly locate an individual's sensitive data, search for the individual by name, or any other identifying detail. The search panelists one or more individuals that match the search criteria. It helps determine the correct individual and then access the detailed view to determine the data stores, schemas, tables, fields, and files that contain the individual's sensitive data.
- Blake is a premium customer. He wants to know where all his data is residing in Customer DATA ASSETS.
- He has submitted a request and the Data Protection Office has forwarded his request to the Data Privacy Management Administrator.
- The Data Privacy Management Administrator will have to generate a report and respond to DPO’s ticket.
Figure 21. Subject Registry
The DSAR report is created and is shown below. The report can be downloaded and can be sent to the customer to get consent on the same. The report is attached to the DPM files provided in the link. (Link needs to be attached to get the sample of the report)
The DSAR report is created and is shown below. The report can be downloaded and can be sent to the customer to get consent on the same. The report is attached to the DPM files provided in the link. (Link needs to be attached to get the sample of the report)
The Data Subject Access Rights report for Blake lists all the Data Sources and sensitive fields associated with him and is listed in this report.
Thus, Mike is now able to generate the report to get consent on the sensitive data.
Figure 22. DSAR Report
How to handle Data Risk:
- Analyze risk based on data properties, policies
- Simulate remediation to understand outcomes
- Track risks by organization, locations, individuals
Now Mike tries to understand how it is moving through the SYSTEM landscape. And he applies the Risk Score, Protection Status, and the Sensitivity Levels. These are obtained from the Data Privacy Management tool integrated with Axon.
Note: The Risk Score, Protection Status, Sensitivity Level will come only when the resource is associated with EDC. As DPM is linked to Axon through EDC, the DPM results are shown only when linked with EDC.
If the EDC license is not available, then it’s better to see the system overlay only.
Figure 23. System Overlay with Risk Scores
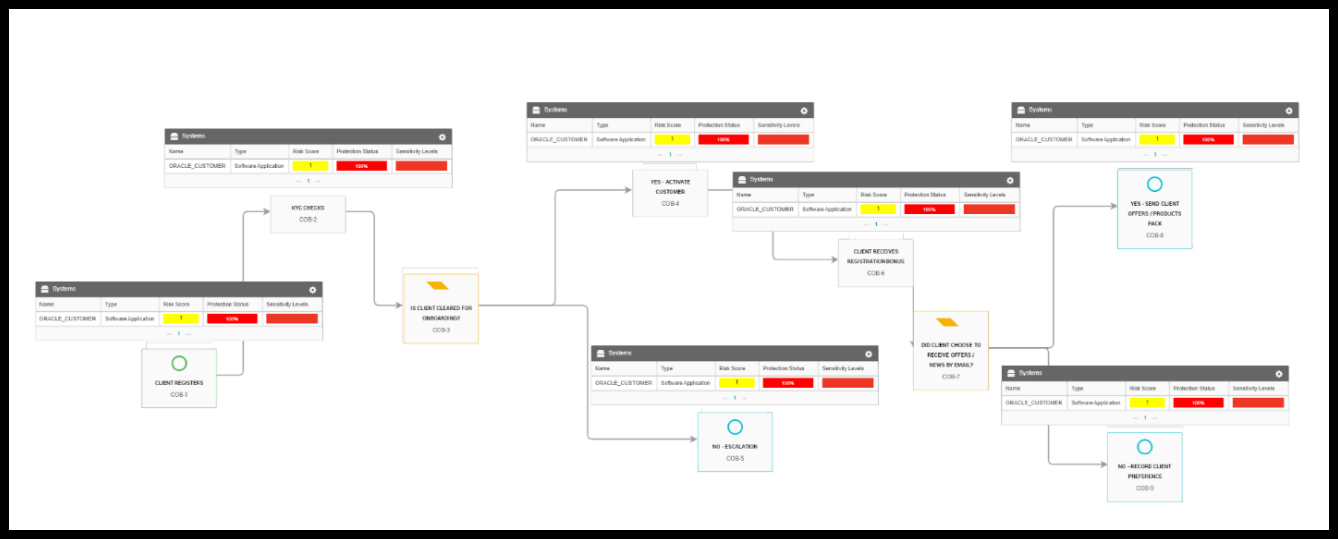
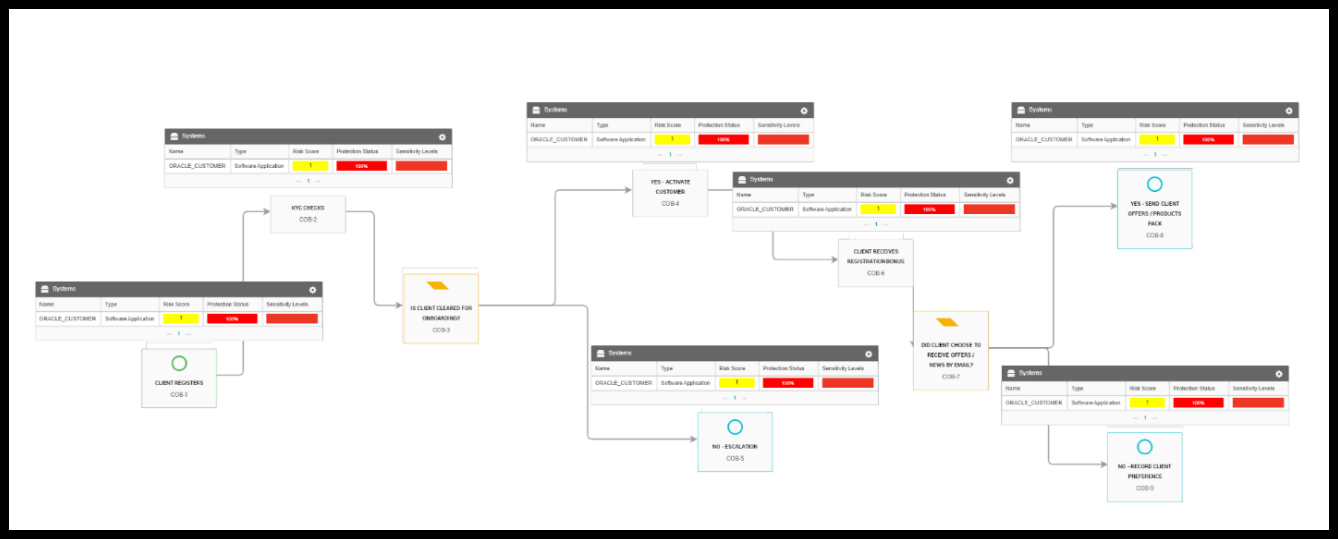
Figure 24. Stakeholder Overlays
And now Mike gets the legal approvals of the data being processed and who it’s being used by, by seeing the overlay of Legal Entity. As per article 30, the organization should know who is using the data and how.
Figure 25. Legal Entities Overlays
Mike thinks whether they have appropriate policies in place as it is going out of the EU. To have good governance the policies must be associated with each process. Now he clicks on the Policies overlay to check what all policies have been aligned to each process. As the KYC check has the special category data to be verified and it is moving out of the EU, he makes sure that the Policy – Processing of Special category data policy is applied.
Figure 26. Policy Overlays
Finally, Mike updates the workflow by seeing the entire process results and how the sensitive data is moving through the COB process and mentions that the sensitive data is moving out of the EU and hence it is required to get the legal approval and necessary precautions to safeguard the Sensitive data and then approve the flow.
Figure 27. Workflow Approval
You can create and manage plans to reduce the risk score and residual risk cost of unprotected sensitive data domains in one or more data stores. For each risk simulation plan, you can adjust the protection status of sensitive data domains in scanned data stores to simulate the impact on the potential cost to your organization in the event of a security breach.
Figure 28. Risk Simulation Plan
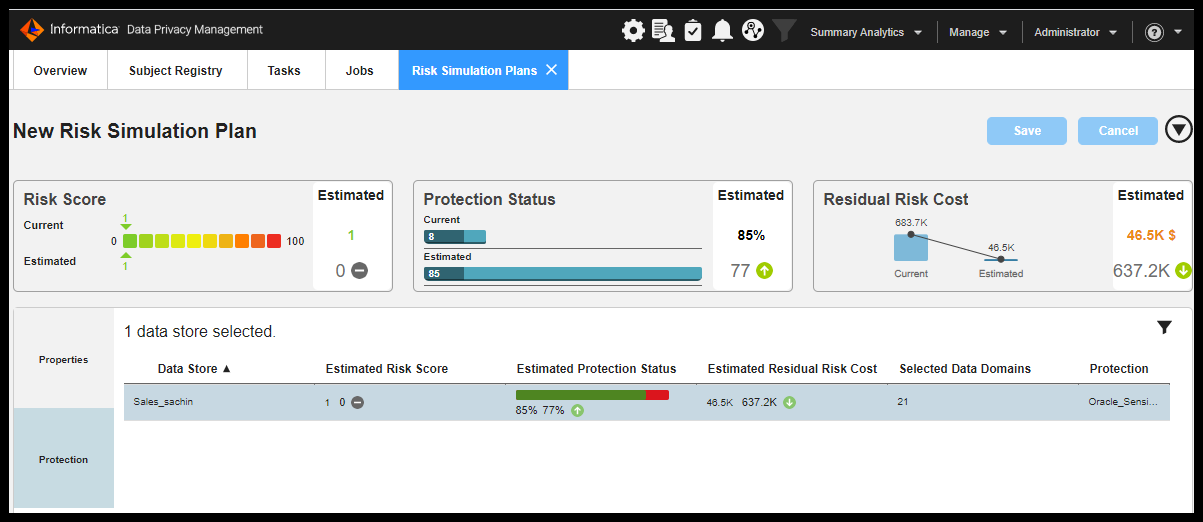
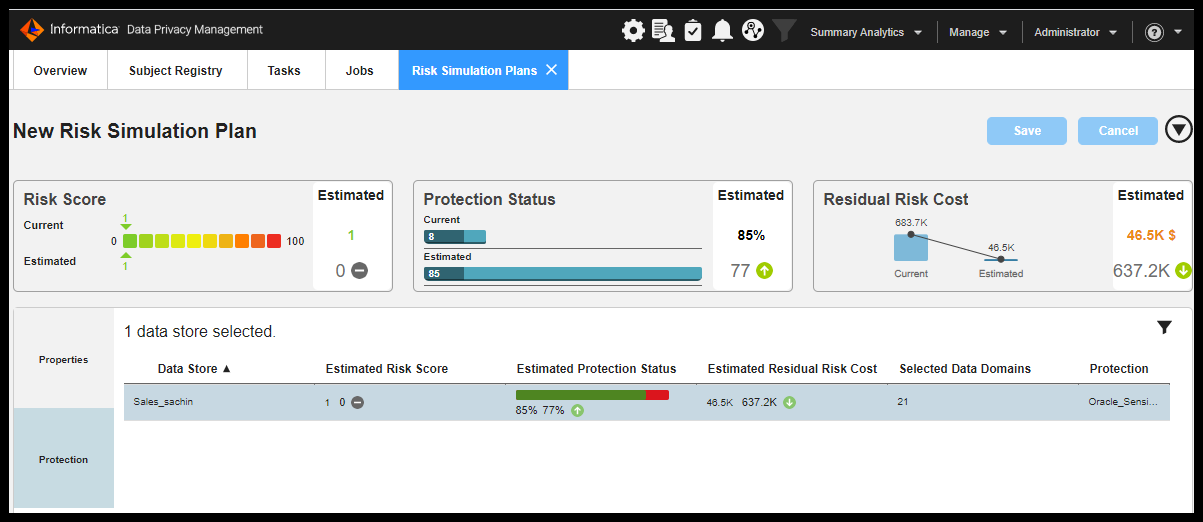
Configure the RISK Simulation plan properties
Configure risk simulation plan protection properties for each datastore included in the plan to reduce the risk score and residual risk cost of unprotected sensitive data.
On the Risk Simulation Plan Details page, you can select sensitive data domains to protect for each scanned data store included in the plan.
The following image shows the risk simulation plan protection properties on the Risk Simulation Plan Details.
Figure 29. Risk Simulation Plan Protection Properties
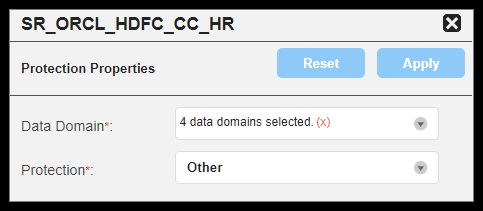
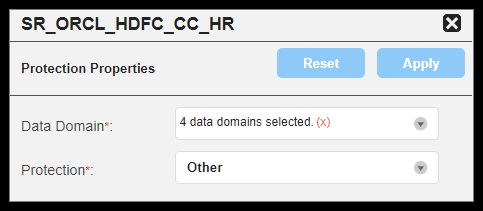
Property |
Description |
Data Domain |
Required. Select one or more sensitive data domains for the selected data store to simulate the impact that protecting data will have on the risk score, protection status, and residual risk cost indicators. |
Protection |
Required. Select a protection method to simulate the risk impact.
|
Based on the assessment of the sensitive data now he plans to mask the data. Now DPO(Otto) asks to protect the sensitive data with the help of DPM and persistence data masking.
How to manage subject rights?
- Implement data protection and monitor for misuse
- Respond to subject rights (i.e. DSAR) and consent requests.
- Communicate remediation, alerts, consent status
A simple diagram shows that once the DSAR report is generated, the consent is taken to protect the data. Even to mask the data or to delete the data or to archive the data the consent is very important as per the GDPR guidelines and policies.
Enacting Consent / Right to be Forgotten
Figure 30. Consent Diagram
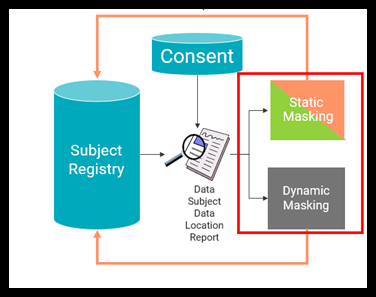
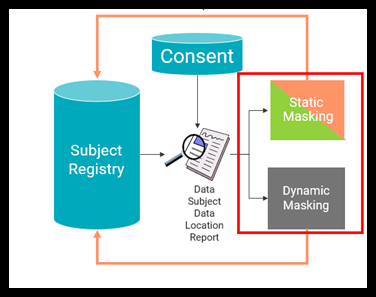
Consent from customers can be taken from third-party tools and Informatica MDM C360. Now Mike knows that with the help of the subject registry, what all the sensitive data and which all tables contain the sensitive data now as per the consent taken, that need to protect data.
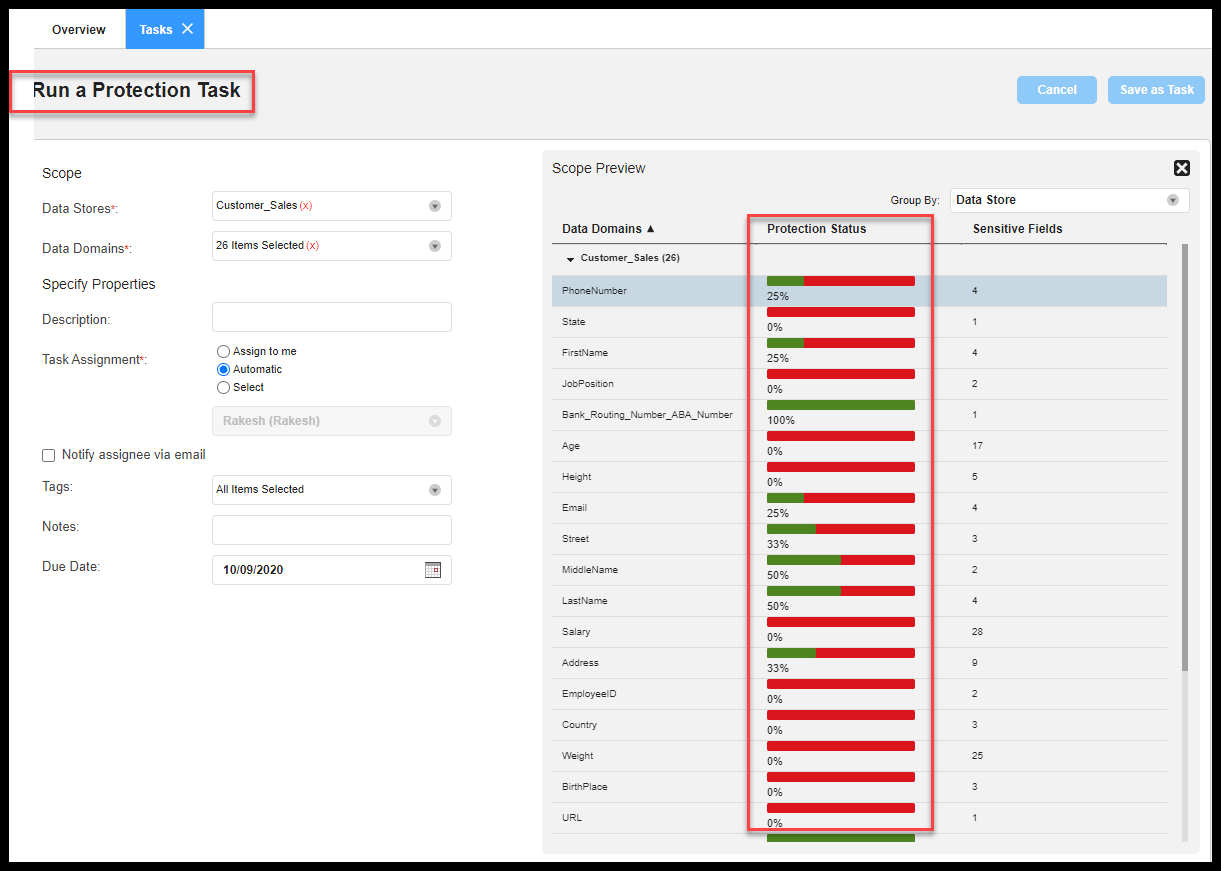
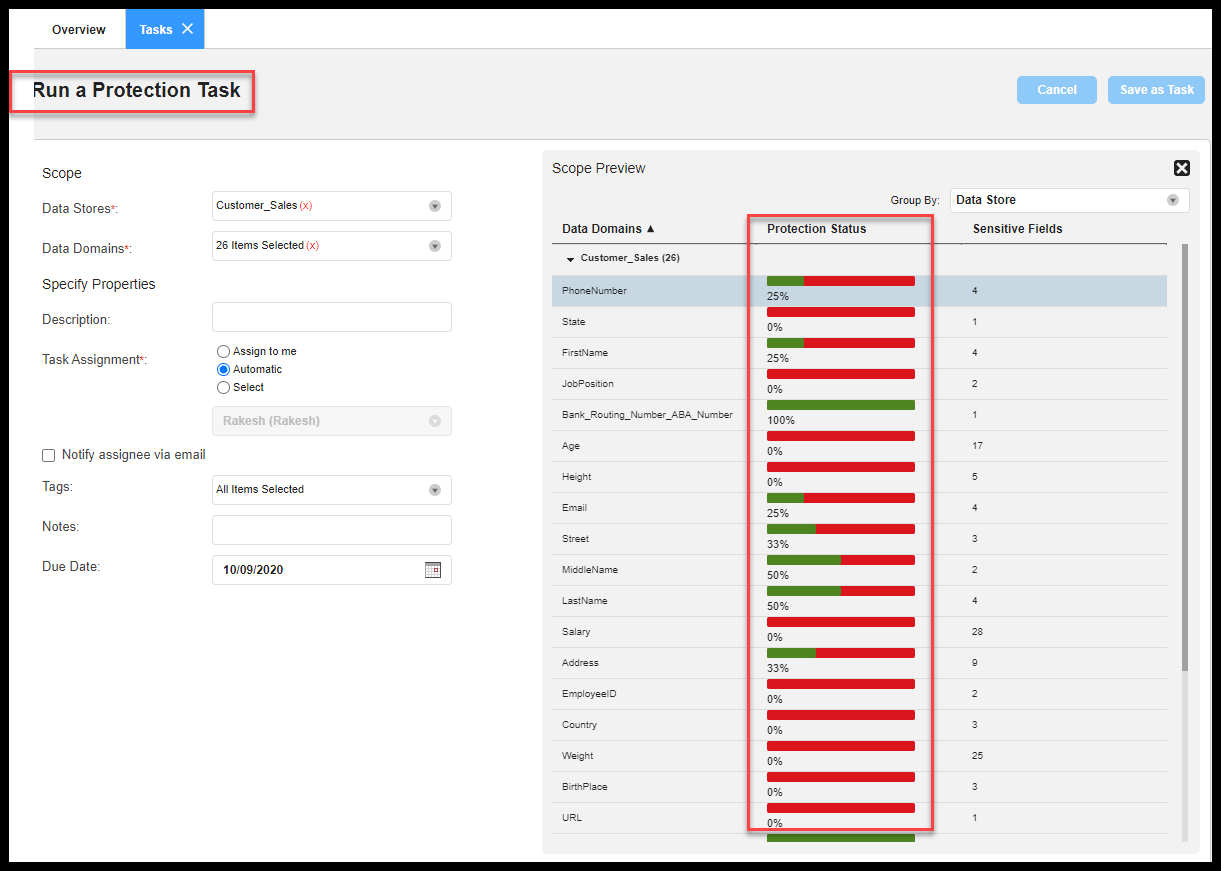
The below screenshot shows the protection status is in ‘Red’ which means there is no protection applied on any sensitive columns. DPO (Otto) logs in to the DPM and sees what all sensitive data is protected.
Figure 31. Protection Status


Figure 32. Protection Task Status
The process which has sensitive data is also captured to see the protection status.
Figure 33. Sensitive Data in Process
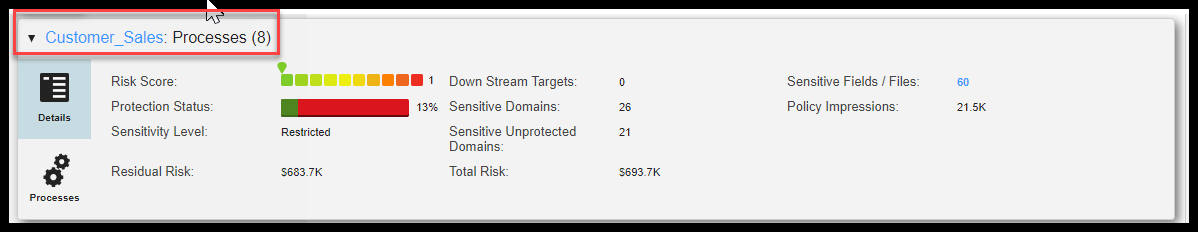
As the DPM is integrated with Axon, the DPO can log into Axon and see the protection status.
Figure 34. Privacy Dashboard in Axon
Now Mike will start the masking process in DPM considering that all the sensitive data should be masked. The below screenshots show the result after the masking rules have been applied.
NOTE: Test data management in connection with DPM helps us to mask the sensitive data and this can be added as extensions in DPM.
Figure 35. Results After Masking
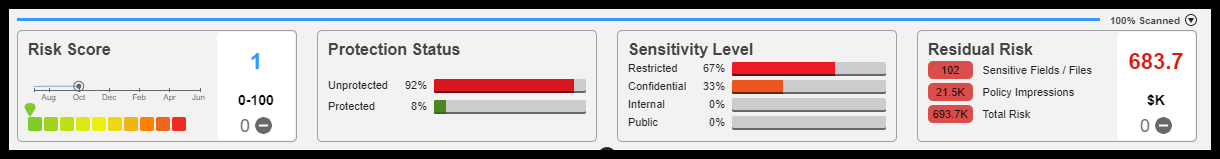
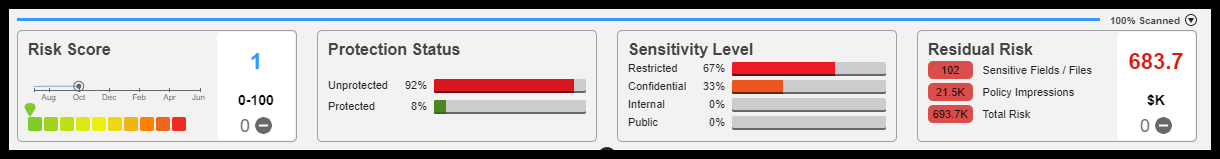
Figure 36. Sensitive Data in Process
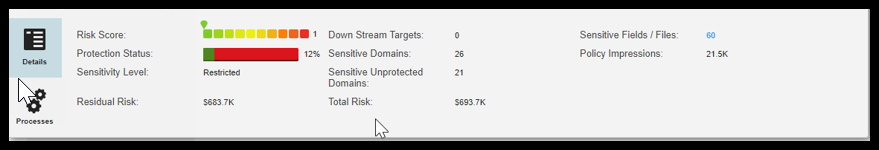
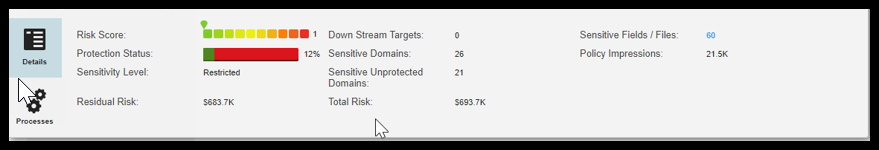
Figure 37. Classification Results


Mike now asks the DPO(Otto) to check the protection status in Axon. Otto now confirms that the protection status is updated for a few sensitive data and updates him ahead for further protecting all the sensitive data.
Figure 38. Privacy Dashboard in Axon after Masking
Finally, the DPO decides after seeing the protection status whether the same can be sent to the customer to get the consent on the sensitive data. Thus, the process of protecting sensitive data is done. DPO now starts looking at getting all the reports and statistics of all the sensitive data that are protected along with the dashboard to update the management.
How to measure Audit Readiness?
- Key risk indicators, visualizations, and reports
- On-Demand reports, drill-downs
DPO (Otto) can see in the DPM that all sensitive data is masked, with the ‘Protected’ columns shown as ‘Yes’.
Figure 39. Protected Results After Masking
After masking the sensitive data now, the system overlays on the Client onboarding process shows the below result.
Note: The same resource is scanned in the DPM to obtain the risk score and protection levels after applying the masking and the results are shown. After obtaining the sensitive data and its security levels, Mike starts masking the data in Data Privacy Management with the help of Persistence Data Masking and the result is extracted in Axon as showed below.
Figure 40. Protected and Sensitive Results of Process Overlays
Finally, the summary of the reports and dashboards.
Figure 41. Summary of Reports and Dashboards
Configuration Video
The GDPR Templates enables your organization to create an integrated operational process for maintaining compliance.
In conclusion, GDPR Compliance is an ongoing commitment. Privacy is going to continue to play an important role for consumers and you need to be ready.
